Page 1 of 2
v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:11 am
by emils
RouterOS version 6.45.1 has been released in public "stable" channel!
Before an upgrade:
1) Remember to make backup/export files before an upgrade and save them on another storage device;
2) Make sure the device will not lose power during upgrade process;
3) Device has enough free storage space for all RouterOS packages to be downloaded.
What's new in 6.45.1 (2019-Jun-27 10:23):
Important note!!!
Due to removal of compatibility with old version passwords in this version, downgrading to any version prior to v6.43 (v6.42.12 and older) will clear all user passwords and allow password-less authentication. Please secure your router after downgrading.
Old API authentication method will also no longer work, see documentation for new login procedure:
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login
MAJOR CHANGES IN v6.45.1:
----------------------
!) dot1x - added support for IEEE 802.1X Port-Based Network Access Control;
!) ike2 - added support for EAP authentication methods (eap-tls, eap-ttls, eap-peap, eap-mschapv2) as initiator;
!) security - fixed vulnerabilities CVE-2018-1157, CVE-2018-1158;
!) security - fixed vulnerabilities CVE-2019-11477, CVE-2019-11478, CVE-2019-11479;
!) security - fixed vulnerability CVE-2019-13074;
!) user - removed insecure password storage;
----------------------
Changes in this release:
*) bridge - correctly display bridge FastPath status when vlan-filtering or dhcp-snooping is used;
*) bridge - correctly handle bridge host table;
*) bridge - fixed log message when hardware offloading is being enabled;
*) bridge - improved stability when receiving traffic over USB modem with bridge firewall enabled;
*) capsman - fixed CAP system upgrading process for MMIPS;
*) capsman - fixed interface-list usage in access list;
*) ccr - improved packet processing after overloading interface;
*) certificate - added "key-type" field;
*) certificate - added support for ECDSA certificates (prime256v1, secp384r1, secp521r1);
*) certificate - fixed self signed CA certificate handling by SCEP client;
*) certificate - made RAM the default CRL storage location;
*) certificate - removed DSA (D) flag;
*) certificate - removed "set-ca-passphrase" parameter;
*) chr - legacy adapters require "disable-running-check=yes" to be set;
*) cloud - added "replace" parameter for backup "upload-file" command;
*) conntrack - fixed GRE protocol packet connection-state matching (CVE-2014-8160);
*) conntrack - significant stability and performance improvements;
*) crs317 - fixed known multicast flooding to the CPU;
*) crs3xx - added ethernet tx-drop counter;
*) crs3xx - correctly display auto-negotiation information for SFP/SFP+ interfaces in 1Gbps rate;
*) crs3xx - fixed auto negotiation when 2-pair twisted cable is used (downshift feature);
*) crs3xx - fixed "tx-drop" counter;
*) crs3xx - improved switch-chip resource allocation on CRS326, CRS328, CRS305;
*) defconf - added "custom-script" field that prints custom configuration installed by Netinstall;
*) defconf - automatically set "installation" parameter for outdoor devices;
*) defconf - changed default configuration type to AP for cAP series devices;
*) defconf - fixed channel width selection for RU locked devices;
*) dhcp - create dual stack queue based on limitations specified on DHCPv4 server lease configuration;
*) dhcp - do not require lease and binding to have the same configuration for dual-stack queues;
*) dhcp - show warning in log if lease and binding dual-stack related parameters do not match and create separate queues;
*) dhcpv4-server - added "client-mac-limit" parameter;
*) dhcpv4-server - added IP conflict logging;
*) dhcpv4-server - added RADIUS accounting support with queue based statistics;
*) dhcpv4-server - added "vendor-class-id" matcher (CLI only);
*) dhcpv4-server - improved stability when performing "check-status" command;
*) dhcpv4-server - replaced "busy" lease status with "conflict" and "declined";
*) dhcpv6-client - added option to disable rapid-commit;
*) dhcpv6-client - fixed status update when leaving "bound" state;
*) dhcpv6-server - added additional RADIUS parameters for Prefix delegation, "rate-limit" and "life-time";
*) dhcpv6-server - added "address-list" support for bindings;
*) dhcpv6-server - added "insert-queue-before" and "parent-queue" parameters;
*) dhcpv6-server - added RADIUS accounting support with queue based statistics;
*) dhcpv6-server - added "route-distance" parameter;
*) dhcpv6-server - fixed dynamic IPv6 binding without proper reference to the server;
*) dhcpv6-server - override prefix pool and/or DNS server settings by values received from RADIUS;
*) discovery - correctly create neighbors from VLAN tagged discovery messages;
*) discovery - fixed CDP packets not including address on slave ports (introduced in v6.44);
*) discovery - improved neighbour's MAC address detection;
*) discovery - limit max neighbour count per interface based on total RAM memory;
*) discovery - show neighbors on actual mesh ports;
*) e-mail - include "message-id" identification field in e-mail header;
*) e-mail - properly release e-mail sending session if the server's domain name can not be resolved;
*) ethernet - added support for 25Gbps and 40Gbps rates;
*) ethernet - fixed running (R) flag not present on x86 interfaces and CHR legacy adapters;
*) ethernet - increased loop warning threshold to 5 packets per second;
*) fetch - added SFTP support;
*) fetch - improved user policy lookup;
*) firewall - fixed fragmented packet processing when only RAW firewall is configured;
*) firewall - process packets by firewall when accepted by RAW with disabled connection tracking;
*) gps - fixed missing minus close to zero coordinates in dd format;
*) gps - make sure "direction" parameter is upper case;
*) gps - strip unnecessary trailing characters from "longtitude" and "latitude" values;
*) gps - use "serial0" as default port on LtAP mini;
*) hotspot - added "interface-mac" variable to HTML pages;
*) hotspot - moved "title" HTML tag after "meta" tags;
*) ike1 - adjusted debug packet logging topics;
*) ike2 - added support for ECDSA certificate authentication (rfc4754);
*) ike2 - added support for IKE SA rekeying for initiator;
*) ike2 - do not send "User-Name" attribute to RADIUS server if not provided;
*) ike2 - improved certificate verification when multiple CA certificates received from responder;
*) ike2 - improved child SA rekeying process;
*) ike2 - improved XAuth identity conversion on upgrade;
*) ike2 - prefer SAN instead of DN from certificate for ID payload;
*) ippool - improved logging for IPv6 Pool when prefix is already in use;
*) ipsec - added dynamic comment field for "active-peers" menu inherited from identity;
*) ipsec - added "ph2-total" counter to "active-peers" menu;
*) ipsec - added support for RADIUS accounting for "eap-radius" and "pre-shared-key-xauth" authentication methods;
*) ipsec - added traffic statistics to "active-peers" menu;
*) ipsec - disallow setting "src-address" and "dst-address" for transport mode policies;
*) ipsec - do not allow adding identity to a dynamic peer;
*) ipsec - fixed policies becoming invalid after changing priority;
*) ipsec - general improvements in policy handling;
*) ipsec - properly drop already established tunnel when address change detected;
*) ipsec - renamed "remote-peers" to "active-peers";
*) ipsec - renamed "rsa-signature" authentication method to "digital-signature";
*) ipsec - replaced policy SA address parameters with peer setting;
*) ipsec - use tunnel name for dynamic IPsec peer name;
*) ipv6 - improved system stability when receiving bogus packets;
*) ltap - renamed SIM slots "up" and "down" to "2" and "3";
*) lte - added initial support for Vodafone R216-Z;
*) lte - added passthrough interface subnet selection;
*) lte - added support for manual operator selection;
*) lte - allow setting empty APN;
*) lte - allow to specify URL for firmware upgrade "firmware-file" parameter;
*) lte - do not show error message for info commands that are not supported;
*) lte - fixed session reactivation on R11e-LTE in UMTS mode;
*) lte - improved firmware upgrade process;
*) lte - improved "info" command query;
*) lte - improved R11e-4G modem operation;
*) lte - renamed firmware upgrade "path" command to "firmware-file" (CLI only);
*) lte - show alphanumeric value for operator info;
*) lte - show correct firmware revision after firmware upgrade;
*) lte - use default APN name "internet" when not provided;
*) lte - use secondary DNS for DNS server configuration;
*) m33g - added support for additional Serial Console port on GPIO headers;
*) ospf - added support for link scope opaque LSAs (Type 9) for OSPFv2;
*) ospf - fixed opaque LSA type checking in OSPFv2;
*) ospf - improved "unknown" LSA handling in OSPFv3;
*) ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066);
*) ppp - added initial support for Quectel BG96;
*) proxy - increased minimal free RAM that can not be used for proxy services;
*) rb3011 - improved system stability when receiving bogus packets;
*) rb4011 - fixed MAC address duplication between sfp-sfpplus1 and wlan1 interfaces (wlan1 configuration reset required);
*) rb921 - improved system stability ("/system routerboard upgrade" required);
*) routerboard - renamed 'sim' menu to 'modem';
*) sfp - fixed S-35LC20D transceiver DDMI readouts after reboot;
*) sms - added USSD message functionality under "/tool sms" (CLI only);
*) sms - allow specifying multiple "allowed-number" values;
*) sms - improved delivery report logging;
*) snmp - added "dot1dStpPortTable" OID;
*) snmp - added OID for neighbor "interface";
*) snmp - added "write-access" column to community print;
*) snmp - allow setting interface "adminStatus";
*) snmp - fixed "send-trap" not working when "trap-generators" does not contain "temp-exception";
*) snmp - fixed "send-trap" with multiple "trap-targets";
*) snmp - improved reliability on SNMP service packet validation;
*) snmp - properly return multicast and broadcast packet counters for IF-MIB OIDs;
*) ssh - accept remote forwarding requests with empty hostnames;
*) ssh - added new "ssh-exec" command for non-interactive command execution;
*) ssh - fixed non-interactive multiple command execution;
*) ssh - improved remote forwarding handling (introduced in v6.44.3);
*) ssh - improved session rekeying process on exchanged data size threshold;
*) ssh - keep host keys when resetting configuration with "keep-users=yes";
*) ssh - use correct user when "output-to-file" parameter is used;
*) sstp - improved stability when received traffic hits tarpit firewall;
*) supout - added IPv6 ND section to supout file;
*) supout - added "kid-control devices" section to supout file;
*) supout - added "pwr-line" section to supout file;
*) supout - changed IPv6 pool section to output detailed print;
*) switch - properly reapply settings after switch chip reset;
*) tftp - added "max-block-size" parameter under TFTP "settings" menu (CLI only);
*) tile - improved link fault detection on SFP+ ports;
*) tr069-client - added LTE CQI and IMSI parameter support;
*) tr069-client - fixed potential memory corruption;
*) tr069-client - improved error reporting with incorrect firware upgrade XML file;
*) traceroute - improved stability when sending large ping amounts;
*) traffic-generator - improved stability when stopping traffic generator;
*) tunnel - removed "local-address" requirement when "ipsec-secret" is used;
*) userman - added support for "Delegated-IPv6-Pool" and "DNS-Server-IPv6-Address" (CLI only);
*) w60g - do not show unused "dmg" parameter;
*) w60g - prefer AP with strongest signal when multiple APs with same SSID present;
*) w60g - show running frequency under "monitor" command;
*) winbox - added "System/SwOS" menu for all dual-boot devices;
*) winbox - do not allow setting "dns-lookup-interval" to "0";
*) winbox - show "LCD" menu only on boards that have LCD screen;
*) wireless - fixed frequency duplication in the frequency selection menu;
*) wireless - fixed incorrect IP header for RADIUS accounting packet;
*) wireless - improved 160MHz channel width stability on rb4011;
*) wireless - improved DFS radar detection when using non-ETSI regulated country;
*) wireless - improved installation mode selection for wireless outdoor equipment;
*) wireless - set default SSID and supplicant-identity the same as router's identity;
*) wireless - updated "china" regulatory domain information;
*) wireless - updated "new zealand" regulatory domain information;
*) www - improved client-initiated renegotiation within the SSL and TLS protocols (CVE-2011-1473);
What's new in 6.45 (2019-Jun-21 09:00):
(factory only release)
What's new in 6.44.4 (2019-May-09 12:14):
(factory only release)
To upgrade, click "Check for updates" at /system package in your RouterOS configuration interface, or head to our download page:
http://www.mikrotik.com/download
If you experience version related issues, then please send supout file from your router to
support@mikrotik.com. File must be generated while router is not working as suspected or after some problem has appeared on device
Please keep this forum topic strictly related to this particular RouterOS release.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:27 am
by amt
many thanks Mikrotik Team...
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:32 am
by Kindis
Wow 9 CVE fixed! Very nice will try this one on the test systems asap!
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:59 am
by ErfanDL
thanks for this Big Update!!! updated RB2011UiAS2HnD and RB951Ui and hAP Lite without any problem.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:14 am
by roe1974
found this in change log:
*) rb4011 - fixed MAC address duplication between sfp-sfpplus1 and wlan1 interfaces (wlan1 configuration reset required);
how todo "wlan1 configuration reset required" ???
regards, Richard
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:15 am
by freemannnn
- cloud - added "replace" parameter for backup "upload-file" command;
what is the correct syntax to replace file? wiki is not updated yet.
please add backup and restore function in winbox.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:24 am
by strods
ros1974 - Command is "/interface wireless reset-configuration"
freemannnn - Here is an example "/system backup cloud upload-file action=create-and-upload replace=cloud-XXXXXXXX-XXXXXX password=123"
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:32 am
by paulct
*) ethernet - added support for 25Gbps and 40Gbps rates
soon, mmmm
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:34 am
by ludvik
What bug exactly is solved by: *) ccr - improved packet processing after overloading interface;
thanks
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:41 am
by ndbjorne
!) security - fixed vulnerabilities CVE-2018-1157, CVE-2018-1158;
https://blog.mikrotik.com/security/secu ... nable.html: All of the above issues are fixed in the following RouterOS releases: 6.42.7, 6.40.9, 6.43
Fixed again?
!) security - fixed vulnerabilities CVE-2019-11477, CVE-2019-11478, CVE-2019-11479;
!) security - fixed vulnerability CVE-2019-13074;
!) user - removed insecure password storage;
*) conntrack - fixed GRE protocol packet connection-state matching (CVE-2014-8160);
*) ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066);
*) www - improved client-initiated renegotiation within the SSL and TLS protocols (CVE-2011-1473);
When in the bugfix?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 12:08 pm
by roe1974
@strods
when i perfom a "/interface wireless reset-configuration" then all my wireless settings are gone?
I have same MAC adress on SFP+ and WLAN Interface 5G (QCA9984) ..... the 2.4GHz Interface has another MAC Adress.
The SFP+ Port is disabled, so do i need to do any changes/resets ?
regards, Richard
PS: can i only reset the config from WLAN 5G ?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 12:30 pm
by grusu
You can try: /interface wireless reset-configuration wlanX where "wlanX" is your 5 GHz wlan interface.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 12:33 pm
by roe1974
wlanX is then the "name" of the interface ?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 12:36 pm
by eworm
I have serve issues with all my IPSec responders. As far as I can tell about half of my IPSec initiator devices do not get addresses from mode-config.
Not sure about the details. Anybody else seen this?
Edit 1:
Initiator devices log:
ipsec,error MikroTik: bad state: 7
Edit 2:
Looking in
/ip ipsec active-peers I noticed those missing
dynamic-address also miss
ph2-total.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 12:58 pm
by roe1974
new change for OVPN:
"ovpn - added "verify-server-certificate" parameter for OVPN client"
how ist he config line for the client ?
regards, Richard
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 1:00 pm
by pacman88
does "improved switch chip allocation" fix the port flapping mentioned in this topic
viewtopic.php?f=2&t=141633 ?
BR
Alex
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 1:00 pm
by mrz
@roe1974 Simple:
verify-server-certificate=yes
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 1:04 pm
by roe1974
that's an config option for the client OVPN config file ??
there is notthing about here of such a config option:
https://openvpn.net/community-resources/how-to/
or is this an option to be set at the OVPN Server on the mikrotik router ?
regards Richard
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 1:06 pm
by mrz
That is an option for RouterOS OVPN clients, for which this exact change apply. It has nothing to do with non-RouterOS OVPN client.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 1:36 pm
by kobuki
Will CVE fixes get into the 6.43 LTS version?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 1:40 pm
by nmt1900
Upgrade 6.44.3 -> 6.45.1
ARP in reply-only mode was used and static ARP entries had to be removed and added back to regain L3 access to other Mikrotik devices on the network (static IP addresses and these same static ARP entries).
RB750Gr3
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:04 pm
by raystream
Upgrade 6.44.3 -> 6.45.1
on my hAP ac lite and on RB2011iL all went fine.
but i have a problem with my RB3011.
I can not login anymore with winbox ("wrong username or password").
All other services are disabled so only connection with winbox possible.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:06 pm
by Chupaka
WinBox version?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:06 pm
by mrz
What winbox version?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:09 pm
by raystream
actual winbox version 3.18
i connected with that winbox version to start the upgrade and after the upgrade the failure happens
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:15 pm
by grusu
wlanX is then the "name" of the interface ?
Yes. In my case wlan 5GHz interface is called "wlan5":
wlan.PNG
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:21 pm
by raystream
i have found the failure.
connecting with the android app over vpn (i am not at home) is fine.
connecting with winbox from my windows laptop over vpn is fone too.
only winbox running with wine on my macbook shows this failure
and after deleting the cache in winbox it connects again on my macbook
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:34 pm
by nichky
i upgrade my RB433AH after that...i couldn't access with current user and password and with admin????
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:40 pm
by LetMeRepair
Same here, hAP ac² ...upgrade from 6.43.2 to 6.45.1 .. .wrong username/password!!
EDIT: clearing Winbox cache (regular Windows 10 / 1903 ) solved issue. Phewww ... that was close.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:42 pm
by proximus
i upgrade my RB433AH after that...i couldn't access with current user and password and with admin????
.
My observation is that after a reboot, the first login attempt fails ... subsequent logins are successful. This behavior has been reproducible after every reboot, of the single device I'm testing on (hAP Lite).
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:46 pm
by nichky
it is my remote site!!!!!
any bug make sense....this one...hhhhhh
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:51 pm
by matiaszon
After swtiching from 6.43.16 to 6.54.1 I am not able to use my LTE connection. My main router (RB2011) is getting an IP from BaseBox2 + R11e-LTE (passthorugh, using only Band 3, T-Mobile Poland). Modem shows status connected and everything seems to be OK. However, there is no traffic coming through LTE modem. I have upgraded Routerbord too and it hasn't helped. After coming back to 6.43.16 it works fine again.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 2:55 pm
by Cha0s
i upgrade my RB433AH after that...i couldn't access with current user and password and with admin????
.
My observation is that after a reboot, the first login attempt fails ... subsequent logins are successful. This behavior has been reproducible after every reboot, of the single device I'm testing on (hAP Lite).
I confirm this behavior. Tested on over 10 installations so far. All had the exact behavior you described.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:00 pm
by Reinis
!) security - fixed vulnerabilities CVE-2018-1157, CVE-2018-1158;
Fixed again?
Both CVE's were fixed in the previous versions, but they could be reproduced differently if you had access to the www service and user account with "full" rights. We have removed this possibility as well.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:01 pm
by nichky
!) security - fixed vulnerabilities CVE-2018-1157, CVE-2018-1158;
Fixed again?
Both CVE's were fixed in the previous versions, but they could be reproduced differently if you had access to the www service and user account with "full" rights. We have removed this possibility as well.
and how can we get access?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:13 pm
by toxmost
PLEASE HELP!!!
I have RB4011iGS+5HacQ2HnD with dlink DPN-100 (TW2362H-CDEL-CLX) GPON SFP module (WAN).
IP address receive via DHCP. ALL WORK GREAT! ---> firmware 6.44.3
If im update firmware to 6.45.1, SFP module have status "link ok", but DHCP address not received, DHCP client all time in status "searching", packet (in module window) TXed, but not RXed.
Help me PLEASE!
Thank you.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:15 pm
by normis
and how can we get access?
You can't

That is the point of this issue. Only the admin himself could trigger the problem. it's not a serious issue, but we still fixed it.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:21 pm
by Stanleyssm
Hi Guys
I am having problem to update my device,
it complete and reboot , but when i go to check the currentversion, is still 6.42 and not 6.45
Please Help
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:21 pm
by nichky
and how can we get access?
You can't

That is the point of this issue. Only the admin himself could trigger the problem. it's not a serious issue, but we still fixed it.
So we have to replace the router? so fany

Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:22 pm
by Stanleyssm
Hy Guys
I try Update , itdomy device downlo and install, then reboot the device...but when i went to check if theCurrent Version of the Update is still 6.42.6. any help
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:25 pm
by nichky
The only access i can get is via SSH. and i downgrade to 6.44.3,nothing happens
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:35 pm
by SimWhite
GRE tunnels won't start anymore between 6.45.1 versions. But 6.44.3 <--> 6.45.1 are working fine.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:43 pm
by normis
and how can we get access?
You can't

That is the point of this issue. Only the admin himself could trigger the problem. it's not a serious issue, but we still fixed it.
So we have to replace the router? so fany

What are you even talking about ? No, you don't have to replace anything. You have no risk here unless you plan to hack your own devices. Please read carefully.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 3:54 pm
by 3bs
After upgrade map receive "ERROR: wrong username or password" when connect with winbox. But connect with webfig, ssh without errors. Clear winbox cache don't helped.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 4:08 pm
by normis
Upgrade Winbox too
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 4:11 pm
by 3bs
winbox version 3.18
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 4:17 pm
by eworm
GRE tunnels won't start anymore between 6.45.1 versions. But 6.44.3 <--> 6.45.1 are working fine.
Is this just GRE or GRE over IPSec? Possibly an IPSec issue?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 4:25 pm
by SimWhite
Is this just GRE or GRE over IPSec? Possibly an IPSec issue?
Both.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 4:37 pm
by Vlad2
After upgrade map receive "ERROR: wrong username or password" when connect with winbox. But connect with webfig, ssh without errors. Clear winbox cache don't helped.
Connect through Winbox again and the second time should already log in normally.
I only have 2 routers so it was, clicked Connect and logged in to the router
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 4:58 pm
by 3bs
Connect through Winbox again and the second time should already log in normally.
I only have 2 routers so it was, clicked Connect and logged in to the router
Tried many times from several machines (win10, winxp), same error. I have more than 15 mikrotik routers, problem only with map2n.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 5:50 pm
by rifkytech
After upgrade map receive "ERROR: wrong username or password" when connect with winbox. But connect with webfig, ssh without errors. Clear winbox cache don't helped.
me to, but i have problem on api, i can connect with winbox, but i can't login with API ( wrong password ). why?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:16 pm
by nuffrespect
GRE tunnels won't start anymore between 6.45.1 versions. But 6.44.3 <--> 6.45.1 are working fine.
Is this just GRE or GRE over IPSec? Possibly an IPSec issue?
The same bug...
IPSec (transport + 47 proto) in established state, phases normal.
GRE tunnels was in down state in 6.45.1 (not running interface)
Downgrade to 6.44.3 - flushed! any settings in Policy
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:33 pm
by nuffrespect
2 Mikrotik Team
Do you confirm some troubles with GRE interfaces + IPSec (transport) ?
What we have to do in that case?
Maybe there is something special with update? For example: We have to update passive sites first to 6.45.1 and after main router to 6.45.1
Or another way?
Thanks!
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:38 pm
by Chupaka
me to, but i have problem on api, i can connect with winbox, but i can't login with API ( wrong password ). why?
Do you use new login style in API?
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:40 pm
by sterod
After upgrade map receive "ERROR: wrong username or password" when connect with winbox. But connect with webfig, ssh without errors. Clear winbox cache don't helped.
I'm having the exact same problem with an RB4011iGS+5HacQ2HnD. Using winbox 3.18, cleared cache, made a dozen login attempts, no joy. This configuration has been in place for months and has now stopped working after upgrading the device to 6.45.1
I am trying to connect to this device through an unencrypted L2TP tunnel with address 172.16.1.5. It simply will not connect through winbox. I can only connect through telnet, therefore I know for certain the username and password are still good. I used a computer that is on the same network as the RB4011 and it is able to connect to winbox using the same username and password with no issue, over the wifi. Therefore, it appears that there is a problem authenticating through winbox when traversing a L2TP tunnel.
EDIT: I've tried PPTP, enabled IPsec on the L2TP tunnel, blanked the admin user password, created a new user with admin, all with no change, the same issue persists.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:43 pm
by Cha0s
2 Mikrotik Team
Do you confirm some troubles with GRE interfaces + IPSec (transport) ?
What we have to do in that case?
Maybe there is something special with update? For example: We have to update passive sites first to 6.45.1 and after main router to 6.45.1
Or another way?
Thanks!
I have IPsec tunnels between 6.45.1 and various 6.4X versions and also all the way back to 5.26.
All IPsec tunnels work without any issues on all versions I have atm.
The only issue I had was that some statically defined policies, lost their peer association after the update. By selecting the correct one, the IPsec sessions established fine.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:58 pm
by nuffrespect
I have IPsec tunnels between 6.45.1 and various 6.4X versions and also all the way back to 5.26.
All IPsec tunnels work without any issues on all versions I have atm.
The only issue I had was that some statically defined policies, lost their peer association after the update. By selecting the correct one, the IPsec sessions established fine.
Yes, i wrote that IPSec was in normal state. May be if you use pure IPsec - that's OK
But in our organization we use GRE tunnels (interface extIP<->extIP) + IPSec in transport mode 47 protocol
(not IPSec SITE2SITE tunnel)
After upgrade remote site to 6.45.1 - router lost some params in Policy. OK. I changed peer's settings. IPSEC state became normal.
BUT GRE interface was in down state, anyway
That's why i decided to made downgrade, until additional info about this.
One brick better, than a lot of bricks, i think.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 6:59 pm
by wpeople
OSPF (over openvpn tunnel) caused me 100% cpu load. Downgrading and all OK.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 7:00 pm
by Cha0s
My configurations use all types of tunnels.
GRE, IPIP, EoIP. All of them, over IPsec without any problems on my end.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 7:03 pm
by osc86
My configurations use all types of tunnels.
GRE, IPIP, EoIP. All of them, over IPsec without any problems on my end.
same here, no issues.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 7:05 pm
by nuffrespect
My configurations use all types of tunnels.
GRE, IPIP, EoIP. All of them, over IPsec without any problems on my end.
Thanks, will try to find out, what's wrong with my situation.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 7:49 pm
by SimWhite
I just tried to create GRE-tunnel without IPsec between 6.45.1 versions on external IPs and disabled firewalls. GRE interface gets the "running" state on the one side but on the other side it does not start. When the 6.44.3 on the other side everything is working fine. CHR is used on the side which won't start.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 8:00 pm
by nuffrespect
My configurations use all types of tunnels.
GRE, IPIP, EoIP. All of them, over IPsec without any problems on my end.
Thanks, will try to find out, what's wrong with my situation.
Something strange. MAIN router at 6.44.3
Try to update 6.45.1 remote sites
On some remote router (mipsbe w|o wireless) on 6.45.1 i see 47 gre in Connection tracker > Tunnes UP
On another remote router (mipsbe + wireless) - nothing -> no gre in Connection tracker with 6.45.1. > Tunnels DOWN
IPIP - works normal on 6.45.1 on failed router
After downgrade failed remote router to 6.44.3 - GRE works normal.
Now see 47 proto in Connection tracker. Tunnels - UP
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 8:01 pm
by eddieb
updating to 6.45.1 went smooth ... from 6.44.3 to 6.45.1 with some help from the dude

No problems so far
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 8:09 pm
by SimWhite
On another remote router (mipsbe + wireless) - nothing -> no gre in Connection tracker with 6.45.1. > Tunnels DOWN
The same on the CHR side.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 8:12 pm
by nuffrespect
Try to update 6.45.1 remote sites
On some remote router (mipsbe w|o wireless) on 6.45.1 i see 47 gre in Connection tracker > Tunnes UP
UPDATE:
NOW Checked Connection tracker -
Tunnels UP - NO GRE 47 protocol in Connection Tracker!
Downgrade last failed router.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 8:27 pm
by bleblas
i have this same problem with API after update to 6.45.1, it's work on 6.44.5 fine.
i update/change login metod before,and i get wrong password
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:00 pm
by marcperea
Hello,
I too am having problems with our software logging in using API. I can SSH and Winbox, but over API we get authentication error - invalid credentials!
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:13 pm
by w0lt
Try to update 6.45.1 remote sites
On some remote router (mipsbe w|o wireless) on 6.45.1 i see 47 gre in Connection tracker > Tunnes UP
UPDATE:
NOW Checked Connection tracker -
Tunnels UP - NO GRE 47 protocol in Connection Tracker!
Downgrade last failed router.
My EoIP tunnels (IPSec) won't come up either. I've tried several methods but no joy. Back to 6.44.3 which works just fine.
-tp
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:15 pm
by dhoulbrooke
Hi All,
For those having trouble with EoIP/GRE following the upgrade the below workaround worked for me:
/ip firewall raw add action=notrack chain=prerouting protocol=gre
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:23 pm
by tesme33
Hi
upgraded crs326 and one hap lite without issues : 6.43.3 --> 6.45.1
one hap lite wont upgrade. I suspect space problem, but there are no files on the system.
[admin@haplite1] > /system resource print
uptime: 11m54s
version: 6.44.3 (stable)
build-time: Apr/23/2019 12:37:03
free-memory: 7.9MiB
total-memory: 32.0MiB
cpu: MIPS 24Kc V7.4
cpu-count: 1
cpu-frequency: 650MHz
cpu-load: 3%
free-hdd-space: 7.5MiB
total-hdd-space: 16.0MiB
write-sect-since-reboot: 709
write-sect-total: 281833
bad-blocks: 0%
architecture-name: smips
board-name: hAP lite
platform: MikroTik
[admin@haplite1] > /file print
# NAME TYPE SIZE CREATION-TIME
0 96N6-4YZ6.key .key file 204 may/26/2019 09:00:16
1 skins directory jan/01/1970 02:00:01
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:27 pm
by anav
I am using capAC in AP WISP Mode and for some reason it does not have access to the internet (probably how I setup my vlans). Two questions.
(1) What method can I use to manually upload the package (dont see a selection in packages)?? and
(2) Should I change the capAC mode to home AP from AP Wisp mode??
NM. No need to change modes in 2, drag and drop works for 1 and reboot.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:32 pm
by TimurA
one hap lite wont upgrade. I suspect space problem.
I confirm. upgrade problem on hap lite.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:47 pm
by UMarcus
one hap lite wont upgrade. I suspect space problem.
I confirm. upgrade problem on hap lite.
My hap lite upgrade with no issues.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 9:56 pm
by mducharme
The API logins were broken in the last beta of 6.45 as well. Is it related to the removal of the old unencrypted password store?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:00 pm
by sebastia
one hap lite wont upgrade. I suspect space problem, but there are no files on the system.
Try upgrading with specific packages that you actually use. So download the "extra packages" and only put the packages you need on device + reboot.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:20 pm
by mserge
Hello,
When i updated my LHG 5 HP, then i couldn't access it by winbox, it says wrong user/pass.
Package is what has been updated however firmware is still on 44.3 as i couldn't access it again to complete the upgrade. Any help please?
Thanks!
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:23 pm
by mkx
Hi
upgraded crs326 and one hap lite without issues : 6.43.3 --> 6.45.1
one hap lite wont upgrade. I suspect space problem, but there are no files on the system.
It's the oroblem with free memory. Devices with small flash (less than 64MB) download upgrade packages to RAM ... and for that some 12MB RAM should be free. Free RAM on your hAP lite is quite low ... do you have some large address list?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:30 pm
by matiaszon
After swtiching from 6.43.16 to 6.54.1 I am not able to use my LTE connection. My main router (RB2011) is getting an IP from BaseBox2 + R11e-LTE (passthorugh, using only Band 3, T-Mobile Poland). Modem shows status connected and everything seems to be OK. However, there is no traffic coming through LTE modem. I have upgraded Routerbord too and it hasn't helped. After coming back to 6.43.16 it works fine again.
nobody can say anything about it?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:31 pm
by OndrejHolas
It seems that archive
all_packages-mmips-6.45.1.zip is truncated on one download server:
https://159.148.147.204/routeros/6.45.1/all_packages-mmips-6.45.1.zip
https://[2a02:610:7501:1000::196]/routeros/6.45.1/all_packages-mmips-6.45.1.zip
Size: 10600448
SHA256: 6c4d219a8e59398c6fe821deec2f12c93bc72adcd1189a02e428a123798414a8 (wrong)
https://[159.148.172.226]/routeros/6.45.1/all_packages-mmips-6.45.1.zip
https://2a02:610:7501:4000::226/routeros/6.45.1/all_packages-mmips-6.45.1.zip
Size: 11811731
SHA256: 2ae2174d31895aeac25afda0a27f22d5394134c0b64bdd34ff10c8a59df83832 (correct)
OH
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:46 pm
by sebastia
After coming back to 6.43.16 it works fine again.
v6.43.16 is using P2P ip configuration for LTE passthrough. 6.45 is using small ip block, back as it was in pre-6.43.
check what ip you get and if you can ping the gateway at least.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:55 pm
by zsolt
I have hAP lite. I want to upgrade from 6.44.3, but not enough flash. The flash-drive is empty (/file print)
Can I remote-upgrade this device?
/system package update install
channel: stable
installed-version: 6.44.3
latest-version: 6.45.1
status: ERROR: not enough disk space, 7.4MiB is required and only 7.3MiB is free
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 10:59 pm
by sebastia
2 options:
1. disable unnecessary packages, and upload ONLY the used ones for upgrade (from "extra packages" zip)
2. netinstall...
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:04 pm
by markos222
someboy could explain me this CVE??
*) conntrack - fixed GRE protocol packet connection-state matching (CVE-2014-8160)
This is not fixed in old versions??
thank you
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:23 pm
by ofer
Upgraded HapACx3 6.43.3 -> 6.45.1 - no issues
Thanks!
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:31 pm
by anav
No issues in upgrading two CapAC and one RB450Gx4.
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:34 pm
by smileymattj
When will the [long-term] receive the CVE fixes addressed in v6.45.1?
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:37 pm
by petrb
FAIL, RB4011, DHCPv6 PD from RADIUS failed, in 6.44.3 works fine. Some ip changed .... I use trick with replace input username in freeradius to pair "mac username" and "Calling-Station-Id"
00:29:47 dhcp,error item: radius authentication failed for f09fc24af7e8 ::/64: prefix changed ::/64 -> 2a01:5e0:30:1000::/60
Workaround:
- Linux with Radius
Framed-IP-Address | = | 192.168.177.15 |
Framed-Route | = | 213.192.5.17/32 192.168.177.15 1 |
Mikrotik-Rate-Limit | = | 5M/5M |
Mikrotik-address-list | = | neplatic |
Calling-Station-Id | = | F0-9F-C2-4A-F7-E8 |
Delegated-IPv6-Prefix | = | 2a01:5e0:30:1000::/60 |
- RB4011 with DHCPv4 and v6
/ip dhcp-server network add address=192.168.177.0/24 dns-server=1.1.1.1 gateway=192.168.177.100
/ipv6 dhcp-server add interface=bridge1 lease-time=10m name=server1 rapid-commit=no use-radius=yes
/radius add address=192.168.43.1 secret=test service=dhcp src-address=10.177.1.1
from radius:
(110) Sent Access-Accept Id 26 from 192.168.43.1:1812 to 10.177.1.1:32839 length 0
(110) Framed-IP-Address = 192.168.177.15
(110) Framed-Route = "213.192.5.17/32 192.168.177.15 1"
(110) Mikrotik-Rate-Limit = "5M/5M"
(110) Mikrotik-Address-List = "neplatic"
(110) Calling-Station-Id = "F0-9F-C2-4A-F7-E8"
(110) Delegated-IPv6-Prefix = 2a01:5e0:30:1000::/60
log in mikrotik:
00:37:41 radius,debug,packet sending Access-Request with id 27 to 192.168.43.1:1812
00:37:41 radius,debug,packet Signature = 0x31ba2d3f58e4837ca33071255ad9bb62
00:37:41 radius,debug,packet NAS-Port-Type = 15
00:37:41 radius,debug,packet NAS-Port = 2199912456
00:37:41 radius,debug,packet Calling-Station-Id = 0xf09fc24af7e8
00:37:41 radius,debug,packet Called-Station-Id = "server1"
00:37:41 radius,debug,packet Delegated-IPv6-Prefix = ::/64
00:37:41 radius,debug,packet User-Name = "F0:9F:C2:4A:F7:E8"
00:37:41 radius,debug,packet User-Password = 0x00000000
00:37:41 radius,debug,packet NAS-Identifier = "RB4011-1"
00:37:41 radius,debug,packet NAS-IP-Address = 10.177.1.1
00:37:41 radius,debug,packet received Access-Accept with id 27 from 192.168.43.1:1812
00:37:41 radius,debug,packet Signature = 0x883ffcd554726f9b161fde42cd81e7ad
00:37:41 radius,debug,packet Framed-IP-Address = 192.168.177.15
00:37:41 radius,debug,packet Framed-Route = "213.192.5.17/32 192.168.177.15 1"
00:37:41 radius,debug,packet MT-Rate-Limit = "5M/5M"
00:37:41 radius,debug,packet MT-Address-List = "neplatic"
00:37:41 radius,debug,packet Calling-Station-Id = "F0-9F-C2-4A-F7-E8"
00:37:41 radius,debug,packet Delegated-IPv6-Prefix = 2a01:5e0:30:1000::/60
00:37:41 radius,debug received reply for 17:22
00:37:41 dhcp,error item: radius authentication failed for f09fc24af7e8 ::/64: prefix changed ::/64 -> 2a01:5e0:30:1000::/60
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:48 pm
by complex1
Upgraded RB4011 from 6.44.3 to 6.45.1 - no issues
Thanks!
Re: v6.45.1 [stable] is released!
Posted: Mon Jul 01, 2019 11:56 pm
by Panbambaryla
Upgraded RB4011 from 6.44.3 to 6.45.1 - no issues
Well, actually there is one - the bridge MAC address has changed so the network discovery on Windows must be done again. In my case the bridge MAC addr is the same as for eth7 interface. Interesting what it depends on...
Best
Bam
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:06 am
by nerxu
ehhhh

lms-notify-sms = DOWN
why - because API has been changed
Now admin says ....: / fuck
say how to fix ?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:09 am
by matiaszon
After coming back to 6.43.16 it works fine again.
v6.43.16 is using P2P ip configuration for LTE passthrough. 6.45 is using small ip block, back as it was in pre-6.43.
check what ip you get and if you can ping the gateway at least.
What do you exactly mean? What should I check? It is not a public IP. What I get is internal IP from my LTE ISP.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:16 am
by STEVEUK1
Has anyone solved these password issues as yet to access the routers ?
We have one remote router which is in a different country. We have a STTP VPN direct to the router which is showing as connected but the username and password are not working - It was working fine before it was upgraded.
It has or at least had a 16 digit random password on it with a custom username.
Tried using the username without a password
Tried the admin account with no password
Tried asking a staff member to reboot it
Still no access and we're not really sure what to try next - Any help much appreciated
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:30 am
by adonato
Hello I have a Router RB 750 and when I tried to update from winbox or donwloading the file from mikrotik
after I rebot, I get this message:
" system,error can not install routeros-mipsbe-6.45.1: it is not made for m
mips, but for mips "
Some know what to do?
Thanks!
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:33 am
by snake27
Hi All,
For those having trouble with EoIP/GRE following the upgrade the below workaround worked for me:
/ip firewall raw add action=notrack chain=prerouting protocol=gre
Thanks!
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:41 am
by w0lt
Hi All,
For those having trouble with EoIP/GRE following the upgrade the below workaround worked for me:
/ip firewall raw add action=notrack chain=prerouting protocol=gre
Good tip !! Got me back up and running with 6.45.1


Thanks !!
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:43 am
by jwilkinson6028
After updating to 6.45.1 I am no longer able to login using the PEAR2 PHP API. Just get an error for login failure in the log.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 1:26 am
by sterod
Has anyone solved these password issues as yet to access the routers ?
We have one remote router which is in a different country. We have a STTP VPN direct to the router which is showing as connected but the username and password are not working - It was working fine before it was upgraded.
It has or at least had a 16 digit random password on it with a custom username.
Tried using the username without a password
Tried the admin account with no password
Tried asking a staff member to reboot it
Still no access and we're not really sure what to try next - Any help much appreciated
I have the same problem, see post #55. I have not found a workaround.
Sent from my Pixel 3 using Tapatalk
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 1:39 am
by STEVEUK1
Has anyone solved these password issues as yet to access the routers ?
We have one remote router which is in a different country. We have a STTP VPN direct to the router which is showing as connected but the username and password are not working - It was working fine before it was upgraded.
It has or at least had a 16 digit random password on it with a custom username.
Tried using the username without a password
Tried the admin account with no password
Tried asking a staff member to reboot it
Still no access and we're not really sure what to try next - Any help much appreciated
I have the same problem, see post #55. I have not found a workaround.
Sent from my Pixel 3 using Tapatalk
Thanks for the response.
Good to know it works on the same network at least - we can get access to a local machine to get on it and downgrade again so we have access, giving us some time to do some testing in the office.
If you do manage to work this out please do let me know - i will of course do the same if we can find a solution.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 2:40 am
by Hyperlight
I had a problem with all my IPSec tunnels for this upgrade. Something is fishy with how the reflexive NAT firewall rule works on the IPSEC initiator side. I had to write a FW rule to allow traffic back in to the initiator from the responder before my GRE tunnels on these interfaces came back up.
The following is what broke, even though tunnel state is established.
IPSec Initiator -> Reponder : Ping Reponder IP - GRE Tunnel Endoint (Works)
IPSec Reponder-> Initiator : Ping Initiator IP GRE Tunnel Endoint (Fails)
Had to write the following FW rule
Accept - Input - External IP of the Responder
After this rule was put in everything came back online. Can someone look into why this rule is now required?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:57 am
by rifkytech
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:58 am
by rifkytech
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:31 am
by elgrandiegote
CHR --> "ERROR: wrong username or password" when I try to login with WinBox 3.18

it is seen that this version was not very tested....
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 5:56 am
by berzerker
!) ike2 - added support for EAP authentication methods (eap-tls, eap-ttls, eap-peap, eap-mschapv2) as initiator;
Since this is "as initiator," can I assume this isn't supported for running as a roadwarrior config?
If so, when is support for that coming, if at all?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:11 am
by lomayani
this release is crashing ccr having vpls tunnels. Downgrading back to 6.44.3 no issue
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:53 am
by strods
ludvik - On some specific and very rare case Ethernet interface on TILE routers could lock up. Now this problem is resolved;
ndbjorne, kobuki, smileymattj - Bugfix version (long-term) will be released as soon as possible;
eworm, matiaszon, toxmost, Stanleyssm, wpeople, petrb, lomayani - I recommend that you provide supout file to
support@mikrotik.com in order to get more information about the problem that you are experiencing;
pacman88 - CRS3xx switches now can better handle traffic passing through the switch if interface speeds are different;
nmt1900 - Can you reproduce this problem once more? Actually. sounds that this was simply a coincidence and the problem was caused by something else besides static ARP entries;
raystream, nichky, LetMeRepair, proximus, Cha0s, 3bs, Vlad2, sterod, mserge, STEVEUK1, elgrandiegote - We can not seem to reproduce the problem with Winbox login. Can you provide more details? From which version did you upgrade your router? Do you, for example, use RADIUS for Winbox authorisation?
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
rifkytech, bleblas, marcperea, mducharme, nerxu, jwilkinson6028 - If you cannot login into your router by using API please make sure that you have updated API authentication script (
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login);
anav - Is this problem related to RouterOS v6.45.1 or this is simply a configuration related question?
OndrejHolas - We will resolve this problem as soon as possible;
markos222 - Currently fix is available only in v6.45. Fix will be backported to long-term versions aswell;
adonato - MIPS and MMIPS are two differnet architectures. Is it RB750 or RB750Gr3? Please name precise model.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:57 am
by mkx
Hello I have a Router RB 750 and when I tried to update from winbox or donwloading the file from mikrotik
after I rebot, I get this message:
" system,error can not install routeros-mipsbe-6.45.1: it is not made for m
mips, but for mips "
Some know what to do?
Which particular RB750 ... the old
RB750UP which is MIPSBE, or the new
hEX (RB750Gr3) which is MMIPS or some other RB750 which might be MIPS? You can check it by running command
/system resource print (it's in the architecture-name field).
Or are you using the built-in way of upgrading (
/system package update install)?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:10 am
by 3bs
raystream, nichky, LetMeRepair, proximus, Cha0s, 3bs, Vlad2, sterod, mserge, STEVEUK1, elgrandiegote - We can not seem to reproduce the problem with Winbox login. Can you provide more details? From which version did you upgrade your router? Do you, for example, use RADIUS for Winbox authorisation?
Upgraded from version 6.44.3, no RADIUS, internal authorisation.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:12 am
by SimWhite
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
GRE up and running now on the both sides.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:31 am
by strods
3bs - Can you please:
1) Try to log into your router by using Winbox;
2) See that authentication fails;
3) Log into your router by another method;
4) Generate supout file;
5) Download file from the router;
6) Send this file to
support@mikrotik.com?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:39 am
by Abdock
Have tried to download few times all_packages-mmips-6.45.1 when extracting it says director is empty.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:59 am
by 3bs
3bs - Can you please:
1) Try to log into your router by using Winbox;
2) See that authentication fails;
3) Log into your router by another method;
4) Generate supout file;
5) Download file from the router;
6) Send this file to
support@mikrotik.com?
Sent.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:03 am
by emils
all_packages-mmips-6.45.1.zip should be working now.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:13 am
by jvparis
Using a SXTsq 5 ac with v6.45.1 the only installation-type that is available when using frequency-mode-regulatory-domain is "outdoors". Can I no longer legally use this device indoors and profit from the wider frequency spectrum? I already know the workaround using superchannel...
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:22 am
by Cetalfio
In the new version of ROS no problem logging on to a RB750 r2 via ssh and Winbox and also mac-telnet, access is right from the local LAN network. If instead I try on an LHG associated as a wireless station to an AP 921, access is possibile only via ssh. Winbox, telnet and mac-telnet do not work the error is: invalid Login and Password.
Cetalfio
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:25 am
by strods
Everyone who is experiencing Winbox login problems, please:
1) Make sure that you use Winbox 3.18;
2) If you use Winbox 3.18, then close all of the Winbox applications (for example, reboot computer) and try again;
3) Check if you can log into your router over WEB interface (Webfig).
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:30 am
by strods
jvparis - Which country have you selected? What happens, if you try to use this command "/interface wireless set [interface_name] country=[your_country] frequency-mode=regulatroy-domain installation=indoor"? What kind of an error do you get?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:36 am
by SimWhite
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
strods, Could you tell is this a bug or a feature? Will it be fixed in the next updates or we should use such kind of rules started from 6.45.1?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:37 am
by jvparis
jvparis - Which country have you selected? What happens, if you try to use this command "/interface wireless set [interface_name] country=[your_country] frequency-mode=regulatroy-domain installation=indoor"? What kind of an error do you get?
Hi strods!
country is germany. This is the error:
[admin@sxt-wds] <SAFE> /interface wireless set wlan1 country=germany frequency-mode=regulatory-domain installation=indoor
failure: allowed installation type is outdoor
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:38 am
by FogOfWar
The login problem is major.
Two LHG-R-s, passwords do not match, even worse, via romon, blank password is accepted although password is set.
Downgraded either to 6.44.3 and 6.44.18 but problem persists. Via romon, password is not accepted, blank password IS accepted.
After logging in, when new terminal is opened, it will fail with wrong password (as it was blank for romon login). correct one is accepted.
Without downgrading, not any password in most interfaces was accepted. Only SSH accepted correct password.
Clear configuration , password change etc. did not change the behaviour.
This password store change needs a rollback ASAP.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:41 am
by petrb
Hi normis,
please explane last line from log. Radius PD DHCPv6, Access-Accept receive but auth failed? What is that? No bindings in dhcpv6. Works in 6.44.3.
00:37:41 radius,debug,packet sending Access-Request with id 27 to 192.168.43.1:1812
00:37:41 radius,debug,packet Signature = 0x31ba2d3f58e4837ca33071255ad9bb62
00:37:41 radius,debug,packet NAS-Port-Type = 15
00:37:41 radius,debug,packet NAS-Port = 2199912456
00:37:41 radius,debug,packet Calling-Station-Id = 0xf09fc24af7e8
00:37:41 radius,debug,packet Called-Station-Id = "server1"
00:37:41 radius,debug,packet Delegated-IPv6-Prefix = ::/64
00:37:41 radius,debug,packet User-Name = "F0:9F:C2:4A:F7:E8"
00:37:41 radius,debug,packet User-Password = 0x00000000
00:37:41 radius,debug,packet NAS-Identifier = "RB4011-1"
00:37:41 radius,debug,packet NAS-IP-Address = 10.177.1.1
00:37:41 radius,debug,packet received Access-Accept with id 27 from 192.168.43.1:1812
00:37:41 radius,debug,packet Signature = 0x883ffcd554726f9b161fde42cd81e7ad
00:37:41 radius,debug,packet Framed-IP-Address = 192.168.177.15
00:37:41 radius,debug,packet Framed-Route = "213.192.5.17/32 192.168.177.15 1"
00:37:41 radius,debug,packet MT-Rate-Limit = "5M/5M"
00:37:41 radius,debug,packet MT-Address-List = "neplatic"
00:37:41 radius,debug,packet Calling-Station-Id = "F0-9F-C2-4A-F7-E8"
00:37:41 radius,debug,packet Delegated-IPv6-Prefix = 2a01:5e0:30:1000::/60
00:37:41 radius,debug received reply for 17:22
00:37:41 dhcp,error item: radius authentication failed for f09fc24af7e8 ::/64: prefix changed ::/64 -> 2a01:5e0:30:1000::/60
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:46 am
by Anumrak
Impossile to upgrade hAP lite. Please fix this. All unnecessary features were disabled. It's not working.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:48 am
by nichky
raystream, nichky, LetMeRepair, proximus, Cha0s, 3bs, Vlad2, sterod, mserge, STEVEUK1, elgrandiegote - We can not seem to reproduce the problem with Winbox login. Can you provide more details? From which version did you upgrade your router? Do you, for example, use RADIUS for Winbox authorisation?
Upgraded from version 6.44.3, no RADIUS, internal authorisation.
Same...Upgraded from version 6.44.3, no RADIUS, internal authorisation.
i upgrade on two devices,on one of them is okay other one no, and i'm not going to upgrade the rest of routers
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:15 am
by Xymox
4011 fail. Sorta. Its remote and started rebooting and being really weird. It would come up and seem fine, but then, go offline again..
For some reason it wont switch back to the partition with 6.44.3 in it. It shows A but when I reboot it does not switch back to it.
Its not up long enough to realy explore what is wrong. I was able to get the config backup off it, so, at least if need be I can setup another and send it out for swap out.
It was set to a higher CPU speed. Which has worked fine for 6 months, going back to the fact CPU speed after the upgrade to 6.45.1 might have fixed it.
Weird issue.
I did upgrade a bunch of CCRs and a few 2011's. No issues.. Just this one 4011..Which was overclocked..
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:31 am
by nmt1900
It looks like Dude has problems with SNMP access.
snmpwalk to other Mikrotik device causes this to appear in log of target device
10:22:24 snmp,debug unsupported v3 security level
10:22:24 snmp,debug v3 err: 0 unsupported security
10:22:24 snmp,debug bad packet
and snmpwalk times out. We have LibreNMS set up for monitoring and
it works fine as it did before.SNMP is set up as v3 private access.
Dude is updated to 6.45.1. It is hard to say whether Dude is the problem or RouterOS on the device itself...
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:34 am
by baragoon
Openvpn broken on v6.45.1. Downgrading back to 6.44.3 and it works.
On client side logs observing this line repeatedly
openvpn[30190]: write to TUN/TAP : Invalid argument (code=22)
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:37 am
by nerxu
Winbox login problem, please:
winbox 3.18 - tools-clear cache WORK
API login problems, please:
change all script (lms,serwer,PHP...) - are you fu... crazy ? I must change all my programs

90% admins says now : F...
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:44 am
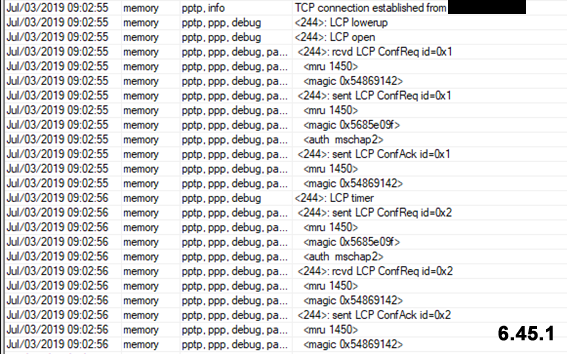
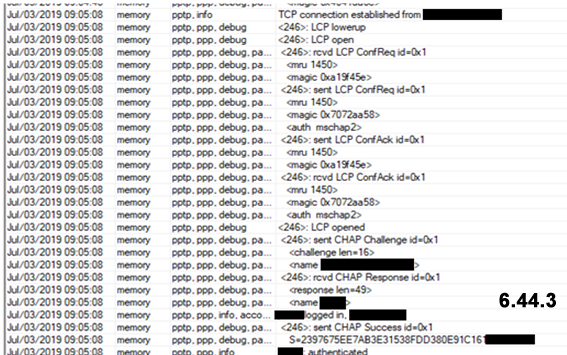
by kanitelka
Hi!
After updating, there was a problem.
I have two incoming channels - main and backup.
VPN (pptp and L2TP)
I can only connect to the backup channel (pptp or l2tp). The port is open on the main channel, the logs are empty
Settings and rules after the update did not change.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:57 am
by bleblas
Winbox login problem, please:
winbox 3.18 - tools-clear cache WORK
API login problems, please:
change all script (lms,serwer,PHP...) - are you fu... crazy ? I must change all my programs

90% admins says now : F...
the problem is, we don't know what we need to change.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:02 am
by WTC
hello,
after upgrade to 6.45.1 we were unable to login to CHR instance(We use it as package source) from clients using System -> AutoUpgrade -> Upgrade Package Sources. In log on CHR we had login failure.
On CHR after downgrade to 6.44.3 and restoring config from backup file. It's working. We won't update clients mikrotiks until this issue is addressed.
thnak you
Michael
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:04 am
by Vlad2
1) (problem with authorization in WinBox after updating to 6.45.1)
And I have the same thing, routers 951, 952, 760. The old RouterBOARD cAP 2n access point and a number of other similar devices.
Radius is not present, settings usual, authorization standard internal, and on a number of devices, after updating - at an input the authorization error was written.
The right to counsel from the team Mikrotik: tried with 3 different computers, all copies of WinBox and closed and opened, two of the 3 computers have to be rebooted. But there is an authorization error (and there is the first time when connecting). Well other users see and read, also the error is present.
Simple decision: 3.19 release WinBox and to upgrade and reset to zero CACHE/cleaned automatically.
2) (problem with not being able to update firmware on RB941)
Hap Lite (RB941) - can't update it, it is to be away, on the disk of the router nothing, no files, no folders. Address-there are no sheets in memory, there is no load on the router. The router was rebooted twice, the error - there is not enough space for updating. I have the feeling(I think) that it is not enough just trivia, 100-150 kilobytes would be removed from the new firmware.
I cannot use NetInstall, the router to be far from me and I consider that the firmware has to be placed on an internal disk of a router and at least still kilobyte 50-90 has to remain. So that am asking team Mikrotik optimize firmware for architecture smips to RB941 can be was renew.
Well, no, so close the model and do not sell it already.
P.S.
People who have RB932 - check, maybe there is a problem with lack of disk space ?
And sorry for bad English
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:05 am
by strods
Everyone who is experiencing problems with Winbox authorization - we will release a new Winbox loader with a fix for this problem as soon as possible. We are very sorry for any inconvenience caused.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:07 am
by llubik
Hapac2 . . . Don't worry me anymore. What version, it infinitely L2TP_IPSec. It's really nervous. Failed to pre-process ph2 packet.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:10 am
by TimurA
People who have RB932 - check, maybe there is a problem with lack of disk space ?
And sorry for bad English
hello, no problem on RB932, only RB941
and
that's where the developers were in a hurry? The problem with the 5ghz interface on the RB4011 has not been resolved. falls.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:16 am
by UMarcus
Upgraded RB4011 from 6.44.3 to 6.45.1 - no issues
Well, actually there is one - the bridge MAC address has changed so the network discovery on Windows must be done again. In my case the bridge MAC addr is the same as for eth7 interface. Interesting what it depends on...
Best
Bam
Here same issue on 3 Devices upgraded from 6.44.3 to 6.45.1.
In my case this cause two major problems :
1. Static DHCP offer of DHCP Server didn't work because of changed MAC -> Login to know IP Address didn't work anymore because get no or a dynamic address from DHCP server
2. The Bridge get the MAC from the WLAN Interface which cause major porblem's in CAPSMAN configuration. There was a lot of 'receive packet from same interface, may loop' messages in the CPASMAN log. The cap client interface's repeatedly connect / disconnect from the CAPSMAN -> WLAN dead
I fix this issue by set the Admin MAC of each bridge manualy.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:16 am
by roe1974
@strods
I have same MAC adress on SFP+ and WLAN Interface 5G (QCA9984) ..... the 2.4GHz Interface has another MAC Adress.
The SFP+ Port is disabled, so do i need to do any changes/resets ?
regards, Richard
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:22 am
by TimurA
@strods
I have same MAC adress on SFP+ and WLAN Interface 5G (QCA9984) ..... the 2.4GHz Interface has another MAC Adress.
The SFP+ Port is disabled, so do i need to do any changes/resets ?
regards, Richard
reset wlan interface configuration
/interface wireless reset-configuration wlan1
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:59 am
by dash
System -> Auto Upgrade feature seems to be broken. Working fine with versions prior to 6.45.
I have a remote Router hosting ROS packages. Other mikrotik routers in the same network are scheduled to check if there is new ROS version on the remote (local network) Mikrotik router. With 6.45 this feature is not working anymore. Clients that want to update cant login anymore. On the remote router I see 'login failures' in the logfile each time a client tries to access it.
Already tried creating a new user and adding group 'full' to it, but with no success...
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:03 pm
by nuffrespect
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
strods, Could you tell is this a bug or a feature? Will it be fixed in the next updates or we should use such kind of rules started from 6.45.1?
The same question, Mikrotik-Team? Bug | Option | ?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:48 pm
by mrz
!) ike2 - added support for EAP authentication methods (eap-tls, eap-ttls, eap-peap, eap-mschapv2) as initiator;
Since this is "as initiator," can I assume this isn't supported for running as a roadwarrior config?
If so, when is support for that coming, if at all?
Road warrior client is always an initiator, so I do not see the reason why it shouldn't be supported.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 12:54 pm
by strods
nuffrespect - Actually bug was the fact that your tunnel did work before. Please see related changelog entry:
"conntrack - fixed GRE protocol packet connection-state matching (CVE-2014-8160)"
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 1:05 pm
by sindy
Actually bug was the fact that your tunnel did work before.
I've always thought that the incoming GRE packets get accepted by the
chain=input action=accept connection-state=established rule because the corresponding connection gets created by the locally originated GRE packet passing through chain output. What's wrong with this idea?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 1:10 pm
by mrz
It is wrong if initiator is remote router.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 1:12 pm
by spacex
It looks like Dude has problems with SNMP access.
snmpwalk to other Mikrotik device causes this to appear in log of target device
10:22:24 snmp,debug unsupported v3 security level
10:22:24 snmp,debug v3 err: 0 unsupported security
10:22:24 snmp,debug bad packet
and snmpwalk times out. We have LibreNMS set up for monitoring and
it works fine as it did before.SNMP is set up as v3 private access.
Dude is updated to 6.45.1. It is hard to say whether Dude is the problem or RouterOS on the device itself...
I have that same problem
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 2:34 pm
by Anumrak
Everyone who is experiencing problems with Winbox authorization - we will release a new Winbox loader with a fix for this problem as soon as possible. We are very sorry for any inconvenience caused.
Hey. What about low capacity of space in hAP lite? Watever I did, it says not enough space. Every time.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 2:46 pm
by serhio
RB1100AHx2 - after upgrade from 6.42.6 > 6.45.1, the router is very unstable. Self reboots on irregular intervals happen.
I tried to disable unnecessary packets (like IPv6, MPLS, Wireless or HotSpot) without any meaningful result.
I sent the email to the support team (with attached support.rif), but no response yet.
I'm considering rollback to 6.43.16 LTS. In addition, I will wait with updates on other devices.
In addition, the IPsec rules aren't transferred automatically and all tunnels went down. I needed to fix all of them manually.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 2:56 pm
by pe1chl
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
I have always had this firewall rule, I presume it is fine as well?
add action=accept chain=input ipsec-policy=in,ipsec protocol=gre
(I have not upgraded yet, running 6.44.3 and this rule as a couple of matches about the same as our number of tunnels)
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:19 pm
by Chupaka
API login problems, please:
change all script (lms,serwer,PHP...) - are you fu... crazy ? I must change all my programs

90% admins says now : F...
If admins don't want to use more secure login - they simply don't upgrade RouterOS versions. If you upgrade RouterOS - what's the problem in upgrading your API library (it should be shared among all your scripts) too?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:23 pm
by adonato
ludvik - On some specific and very rare case Ethernet interface on TILE routers could lock up. Now this problem is resolved;
ndbjorne, kobuki, smileymattj - Bugfix version (long-term) will be released as soon as possible;
eworm, matiaszon, toxmost, Stanleyssm, wpeople, petrb, lomayani - I recommend that you provide supout file to
support@mikrotik.com in order to get more information about the problem that you are experiencing;
pacman88 - CRS3xx switches now can better handle traffic passing through the switch if interface speeds are different;
nmt1900 - Can you reproduce this problem once more? Actually. sounds that this was simply a coincidence and the problem was caused by something else besides static ARP entries;
raystream, nichky, LetMeRepair, proximus, Cha0s, 3bs, Vlad2, sterod, mserge, STEVEUK1, elgrandiegote - We can not seem to reproduce the problem with Winbox login. Can you provide more details? From which version did you upgrade your router? Do you, for example, use RADIUS for Winbox authorisation?
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
rifkytech, bleblas, marcperea, mducharme, nerxu, jwilkinson6028 - If you cannot login into your router by using API please make sure that you have updated API authentication script (
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login);
anav - Is this problem related to RouterOS v6.45.1 or this is simply a configuration related question?
OndrejHolas - We will resolve this problem as soon as possible;
markos222 - Currently fix is available only in v6.45. Fix will be backported to long-term versions aswell;
adonato - MIPS and MMIPS are two differnet architectures. Is it RB750 or RB750Gr3? Please name precise model.
Hello I have a RouterBOARD 750G r3
uptime: 14h59m39s
version: 6.44.3 (stable)
build-time: Apr/23/2019 12:37:03
factory-software: 6.36.1
free-memory: 167.8MiB
total-memory: 256.0MiB
cpu: MIPS 1004Kc V2.15
cpu-count: 4
cpu-frequency: 880MHz
cpu-load: 6%
free-hdd-space: 172.0KiB
total-hdd-space: 16.3MiB
write-sect-since-reboot: 146662
write-sect-total: 84183238
bad-blocks: 0%
architecture-name: mmips
board-name: hEX
platform: MikroTik
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:29 pm
by boquepasha
Greetings!
We've observed similar behaviour with a customer of ours who has a RouterBOARD LHG 5nD, but not quite the same. We had mac-telnet access before upgrading routerOS to 6.45.1. After the upgrade, we can no longer log in by mac-telnet login, but we can through any other method, including Winbox. We've tried disabling and enabling the mac-telnet server to no avail. After downgrading to 6.44.3 (and restoring the missing password) we recovered mac-telnet access, as well as any other acces we had. So far we've stopped our upgrade schedule until this problem gets sorted out.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:35 pm
by elgrandiegote
Hi strods,
i've upgraded several devices from version 6.44.3 (RB3011, RB2011) but the problem is with the CHR, however i can connect via ssh without problem,
I use WinBox 3.18 without RADIUS
regards
ludvik - On some specific and very rare case Ethernet interface on TILE routers could lock up. Now this problem is resolved;
ndbjorne, kobuki, smileymattj - Bugfix version (long-term) will be released as soon as possible;
eworm, matiaszon, toxmost, Stanleyssm, wpeople, petrb, lomayani - I recommend that you provide supout file to
support@mikrotik.com in order to get more information about the problem that you are experiencing;
pacman88 - CRS3xx switches now can better handle traffic passing through the switch if interface speeds are different;
nmt1900 - Can you reproduce this problem once more? Actually. sounds that this was simply a coincidence and the problem was caused by something else besides static ARP entries;
raystream, nichky, LetMeRepair, proximus, Cha0s, 3bs, Vlad2, sterod, mserge, STEVEUK1, elgrandiegote - We can not seem to reproduce the problem with Winbox login. Can you provide more details? From which version did you upgrade your router? Do you, for example, use RADIUS for Winbox authorisation?
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
rifkytech, bleblas, marcperea, mducharme, nerxu, jwilkinson6028 - If you cannot login into your router by using API please make sure that you have updated API authentication script (
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login);
anav - Is this problem related to RouterOS v6.45.1 or this is simply a configuration related question?
OndrejHolas - We will resolve this problem as soon as possible;
markos222 - Currently fix is available only in v6.45. Fix will be backported to long-term versions aswell;
adonato - MIPS and MMIPS are two differnet architectures. Is it RB750 or RB750Gr3? Please name precise model.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:37 pm
by 3bs
Hey. What about low capacity of space in hAP lite? Watever I did, it says not enough space. Every time.
Try uninstall additional packages, then update. After update install packages.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 3:48 pm
by dakotabcn
I have downgraded to 6.44.3 the rb4011 with wifi due fails with L2TP connections
Mi computer connect with any problem, but other users no connect, the log report phase1 negotiation failed
Others router RB3011 have the same issue
All routers have NAT for Inet (the ftth/hfc router is wit NAT) and all computers have win8/10 with nat trasversal
This bug is vert bad, please repair
thx!
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:07 pm
by lenciso
I updated 2 RB2011 and 2 RB951 without problems.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:08 pm
by berzerker
!) ike2 - added support for EAP authentication methods (eap-tls, eap-ttls, eap-peap, eap-mschapv2) as initiator;
Since this is "as initiator," can I assume this isn't supported for running as a roadwarrior config?
If so, when is support for that coming, if at all?
Road warrior client is always an initiator, so I do not see the reason why it shouldn't be supported.
Well, I'm receiving an error trying to add an identity for IKEv2 w/ EAP-TLS authentication, saying it's only supported as a client.
[admin@RB4011] /ip ipsec identity> add peer=ikev2 auth-method=eap eap-methods=eap-tls remote-certificate=ios-client generate-policy=port-strict
failure: only EAP client supported
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:11 pm
by mrz
As far as I understand you are trying to configure server. Server requires RADIUS server with EAP support. Locally on the router it is not supported.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:19 pm
by berzerker
As far as I understand you are trying to configure server. Server requires RADIUS server with EAP support. Locally on the router it is not supported.
Ok...so that goes back to my original question. Will this be supported without the requirement of RADIUS, locally on ROS?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:21 pm
by Gusse
RESOLVED: OVPN Server Binding was causing some issues. I deleted the old one instances and made a new one, then it started to work again.
I noticed issues with Android OpenVPN client after upgrade. Before it worked ok, but now I get this. Log full of this TUN write error.
16:08:56.806 -- EVENT: ASSIGN_IP
16:08:56.884 -- Connected via tun
16:08:56.885 -- EVENT: CONNECTED info='xxxx@xxc.xxx:1194 (xxx.xxx.xxx.xxx) via /TCPv4 on tun/10.0.0.84/ gw=[10.0.0.85/]' trans=TO_CONNECTED
16:09:22.049 -- TUN write error: write_some: Invalid argument
16:09:22.054 -- TUN write error: write_some: Invalid argument
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:22 pm
by enzain
Some routers after upgrade not allow login
Username or password incorrect.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:38 pm
by Cha0s
Everyone who is experiencing problems with Winbox authorization - we will release a new Winbox loader with a fix for this problem as soon as possible. We are very sorry for any inconvenience caused.
While you are at it, will you fix the interfaces last up/down times on winbox that are in the future?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:39 pm
by sindy
It is wrong if initiator is remote router.
Can you be more verbose? "initiator" is a role of an IPsec peer, but there is no "initiator/responder" or "client/server" role related to GRE, both ends of the tunnel are sending no matter whether the remote end responds or not and no matter whether a corresponding IPsec policy is available or not, and no matter what is the role of the IPsec peer used by that policy. As there are no ports in GRE, and as the ID field is the same for all packets, an IP.A (local) ->IP.B (remote) packet passing the output chain should create a tracked connection, so a received packet IP.B->IP.A should match "connection-state=established" in the input chain.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 4:54 pm
by mrz
In terms of connection tracking there will be always the one that initiates/creates (call it whatever you like) new connection. If remote device trying to initiate connection it should not be accepted by "establish/related" rule because connection does not exist yet. That is what happened before the fix.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 5:05 pm
by artem1
After upgrade my CHR on intel with aes-ni to 6.45.1 I see flag "Hardware AEAD" is gray (off) (in IPSEC on installed SA tab).
Before upgrade this flag was shown as enabled (black).
Enc: sha1+aes-cbc128
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 5:08 pm
by petern
Can you be more verbose? "initiator" is a role of an IPsec peer, but there is no "initiator/responder" or "client/server" role related to GRE, both ends of the tunnel are sending no matter whether the remote end responds or not and no matter whether a corresponding IPsec policy is available or not, and no matter what is the role of the IPsec peer used by that policy. As there are no ports in GRE, and as the ID field is the same for all packets, an IP.A (local) ->IP.B (remote) packet passing the output chain should create a tracked connection, so a received packet IP.B->IP.A should match "connection-state=established" in the input chain.
I think you have it the wrong way around. GRE itself may not have initiator/responder terminology, but connection-tracking does. Thus, if the GRE packet first comes from the remote side, you need to explicitly allow it and not rely on established, as it isn't yet an established connection. I've always used an explicit allow rule for this, as that's how it should work.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 5:19 pm
by Anumrak
Hey. What about low capacity of space in hAP lite? Watever I did, it says not enough space. Every time.
Try uninstall additional packages, then update. After update install packages.
This is abnormal behavior. I'll wait for a fix for this.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 5:36 pm
by sindy
In terms of connection tracking there will be always the one that initiates/creates (call it whatever you like) new connection. If remote device trying to initiate connection it should not be accepted by "establish/related" rule because connection does not exist yet. That is what happened before the fix.
OK, so I assume you are saying that if the GRE packet comes from outside first (and, logically, doesn't match
connection-state=established), no outgoing GRE packet will ever be sent because the local side only responds to connection attempts coming from the remote one inside the GRE tunnel, and the GRE packets carrying these connection attempts get dropped.
What about the GRE keepalives then? I've often created GRE tunnels with no actual payload traffic to use them for minutes and they did come up nevertheless, so I've always thought the keepalive packets are what creates the tracked connection.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 6:34 pm
by nmt1900
nmt1900 - Can you reproduce this problem once more? Actually. sounds that this was simply a coincidence and the problem was caused by something else besides static ARP entries
Router has one bridge with 2 addresses/subnets on it without VLANs and ARP in reply-only mode.
Subnet 1 has DHCP with add-arp-for-leases=yes and it is main subnet with client devices in it.
Subnet 2 has only some other devices in it for testing and static ARP entries for these devices in router's ARP list.
This setup worked without problems before, but now there is a problem:
subnet 1 works OK, devices can access each other and public internet and this subnet can be accessed over incoming VPN connection
subnet 2 cannot be accessed from subnet 1 and devices in subnet 2 cannot access router, subnet 1 or public internet. Devices in it cannot be accessed over incoming VPN connection either. Other Mikrotik devices in subnet 2 can only be accessed by MAC telnet or RoMON when problem is present.
Devices from subnet 2 will regain access after their static ARP entries are removed and added back, but after some time problem comes back - just like ARP entries are aged out, but still existing in list.
Everything works OK, when ARP is set to enabled mode.
If ARP is left to reply-only mode and accept rule (subnet 1 and subnet 2 as both source and destination) is added to forward chain, then it looks like this rule also solves the problem. This was not needed before
Long story got shorter - I moved one device with static address and ARP entry from subnet 2 to subnet 1. For some weird reason additional dynamic ARP entry started popping up with old IP address and it did not went away although IP address did not exist at that time. Then I moved this device back to subnet 2 and only the right ARP entry remained. Problem disappeared after that.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:09 pm
by buset1974
i'am having "rebooted without proper shutdown by watchdog timer" again after upgrading to 6.45.1 on CCR-1036-8G-2S+ from 6.44.3
It's has ipv4 and ipv6 running on the routers
We have this kind of issues last years and already fixed and it happen again now, please check my tickets #2018060122002189
Please check what changed on 6.45.1 that caused this happen again.
thx
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:30 pm
by antonina2
Updated the router to the current version.
After the update, we can not work.

LAN computers behind RB951 cannot connect to PPTP servers.
We stopped work. Help.
P.S. Sorry, I know English very bad.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:33 pm
by sindy
Updated the router to the current version.
After the update, we can not work.

LAN computers behind RB951 cannot connect to PPTP servers.
We stopped work. Help.
P.S. Sorry, I know English very bad.
PPTP uses GRE to transport data. If the PPTP connections seem to be up but no data actually pass through them, look earlier in this thread for the firewall rule necessary to allow GRE to work. As the PPTP clients run on the LAN computers, not on the Mikrotik itself, the rule will have to be effective in the forward chain.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:38 pm
by antonina2
PPTP uses GRE to transport data. If the PPTP connections seem to be up but no data actually pass through them, look earlier in this thread for the firewall rule necessary to allow GRE to work. As the PPTP clients run on the LAN computers, not on the Mikrotik itself, the rule will have to be effective in the forward chain.
I tried different rules from this branch, nothing helps. Could you give an example of the rule? Thanks.
1 ;;; defconf: accept established,related,untracked
chain=input action=accept connection-state=established,related,untracked log=no log-prefix=""
2 ;;; defconf: drop invalid
chain=input action=drop connection-state=invalid log=no log-prefix=""
3 ;;; defconf: accept ICMP
chain=input action=accept protocol=icmp
4 ;;; defconf: drop all not coming from LAN
chain=input action=drop in-interface-list=!LAN log=no log-prefix=""
5 ;;; defconf: accept in ipsec policy
chain=forward action=accept log=no log-prefix="" ipsec-policy=in,ipsec
6 ;;; defconf: accept out ipsec policy
chain=forward action=accept log=no log-prefix="" ipsec-policy=out,ipsec
7 ;;; defconf: fasttrack
chain=forward action=fasttrack-connection connection-state=established,related
8 ;;; defconf: accept established,related, untracked
chain=forward action=accept connection-state=established,related,untracked
9 ;;; defconf: drop invalid
chain=forward action=drop connection-state=invalid log=no log-prefix=""
10 ;;; defconf: drop all from WAN not DSTNATed
chain=forward action=drop connection-state=new connection-nat-state=!dstnat in-interface-list=WAN log=no log-prefix=""
11 ;;; Drop BOGONS List
chain=input action=drop src-address-list=BOGONS in-interface-list=WAN log=yes log-prefix=""
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:40 pm
by sindy
Could you give an example of the rule?
/ip firewall filter add chain=forward action=accept protocol=gre src-address=ip.address.of.the.PPTP.server
It must be at the right place in the forward chain. If you're not sure, create a dedicated topic and post the export of your configuration there. See my automatic signature for details.
The rule should be placed between rules 8 and 9 in your
/ip firewall filter print above.
And more than that:
- as we talk about multiple PPTP servers, you probably need to use src-address-list in the rule, which contains addresses of all the servers, not just a single src-address,
- as we talk about the forward chain, you need another rule where the same address-list is used as dst-address-list, as the first packet to be tunneled via GRE may come from either direction.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:47 pm
by jsadler
I also have the Winbox Login Problem that has been mentioned....
I note that this is ***INTERMITTENT*** and so far it seems to only happen on links with higher latency.
I've upgraded approx 20 devices. This may or may not be a coincidence, however I have noted that devices that are nearby to my location are fine (approx 15) and don't have any login issues. Devices which are far away, eg international, or local but via LTE mobile data links (eg high latency) etc seem to have the issue (5 devices)
I've seen the login issue on CHR, LTAP and CRS, so I don't think it matters which hardware variant you are using.
When my login is failing, if I keep clicking connect in Winbox, it will usually connect after 5 to 10 attempts.
Note that the router logs the invalid connection attempt as a login failure for user xyz with the source IP of the winbox client, but other than that nothing else of interest is logged.
Cheers,
Jono.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 7:53 pm
by petrb
DHCPv6 PD with RADIUS not work with dhcp6c in linux/ubnt .... work in 6.44.3. Work with DHCPv6 client with mikrotik. Very simple radius configuration:
744d288d0d1e => Mikrotik DHCPv6 client works (
can fail when prefix is changed and release action is not invoked)
f09fc24af7e8 => UBNT/Ubuntu tested linux dhcp6c FAIL - works in 6.44.3
dhcp,error item: radius authentication failed for f09fc24af7e8 ::/60: prefix changed ::/60 -> 2a01:5e0:31:1000::/60
select * from radcheck
f09fc24af7e8 | Auth-Type | := | Accept
744d288d0d1e | Auth-Type | := | Accept
select * from radreply
f09fc24af7e8 | Delegated-IPv6-Prefix | = | 2a01:5e0:31:1000::/60
744d288d0d1e | Delegated-IPv6-Prefix | = | 2a01:5e0:31:2000::/60
cat /etc/dhcp6c.conf
interface ath0 {
request domain-name-servers;
send ia-na 1;
send ia-pd 1;
script "/usr/bin/dhcp6c-state";
};
id-assoc na 1 {
};
id-assoc pd 1 {
prefix ::/60 infinity;
prefix-interface eth0 {
sla-id 0;
sla-len 4;
};
};
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:21 pm
by nightcom
I see some of you have problems, just to make it more clear below is list of units that I upgraded to 6.45.1 without problems
RB3011UiAS-RM
hex RB750Gr3
Upgraded via Winbox 3.18
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:41 pm
by mserge
Everyone who is experiencing problems with Winbox authorization - we will release a new Winbox loader with a fix for this problem as soon as possible. We are very sorry for any inconvenience caused.
Any news about when will the new winbox be available?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 8:49 pm
by kadety
Some routers after upgrade not allow login
Username or password incorrect.
I have the same problem. RB951G
Username or password incorrect.
Does anyone have a solution? Please
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:10 pm
by antonina2
/ip firewall filter add chain=forward action=accept protocol=gre src-address=ip.address.of.the.PPTP.server
It must be at the right place in the forward chain. If you're not sure, create a dedicated topic and post the export of your configuration there. See my automatic signature for details.
The rule should be placed between rules 8 and 9 in your
/ip firewall filter print above.
And more than that:
- as we talk about multiple PPTP servers, you probably need to use src-address-list in the rule, which contains addresses of all the servers, not just a single src-address,
- as we talk about the forward chain, you need another rule where the same address-list is used as dst-address-list, as the first packet to be tunneled via GRE may come from either direction.
For me it does not work.
Experimentally found out.
We have always been disabled service-port
/ip firewall service-port
set ftp disabled=yes
set tftp disabled=yes
set irc disabled=yes
set h323 disabled=yes
set sip disabled=yes
set pptp disabled=yes
set udplite disabled=yes
set dccp disabled=yes
set sctp disabled=yes
Enabling pptp solved the problem.
Now the clients of the local network can connect to the pptp servers in the Internet.
2
mrz &
strods
This is a bug, or so it is conceived?
Why does this affect forward pptp?
/ip firewall service-port
set pptp disabled=yes
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 9:43 pm
by sindy
This is a bug, or so it is conceived?
Please do read the previous posts of this topic. @strods has already explained that a bug (with its own CVE) was the previous behaviour, where incoming GRE was allowed to pass through the firewall even without a corresponding permissive rule in place.
Why does this affect forward pptp?
/ip firewall service-port
set pptp disabled=yes
It didn't come to my mind you could have the helpers disabled as by default they are enabled, so I was expecting a PPTP helper didn't exist at all, so I've suggested those rules above. My fault.
The whole
/ip firewall service-port section deals with cases where communication using one protocol controls establishment of connections which use another protocol. So the firewall analyses the information in the control protocol and creates a connection-tracking record marked with
connection-state=related in advance, before the first packet of that "controlled" connection arrives. So in the particular case of PPTP, when a PPTP control session between a client and the server gets established inside a TCP session (port 1723 on server side), the PPTP helper in the firewall prepares a tracked GRE connection between the IP addresses of the client and the server, so the rule
action=accept chain=forward connection-state=established,related accepts these packets even though no rule explicitly permitting them exists in the forward chain.
/ip firewall connection-print where protocol~"gre" should show you a connection marked with
E in the attributes column, which means
Expected, which means
connection-state=related.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:07 pm
by adonato
ludvik - On some specific and very rare case Ethernet interface on TILE routers could lock up. Now this problem is resolved;
ndbjorne, kobuki, smileymattj - Bugfix version (long-term) will be released as soon as possible;
eworm, matiaszon, toxmost, Stanleyssm, wpeople, petrb, lomayani - I recommend that you provide supout file to
support@mikrotik.com in order to get more information about the problem that you are experiencing;
pacman88 - CRS3xx switches now can better handle traffic passing through the switch if interface speeds are different;
nmt1900 - Can you reproduce this problem once more? Actually. sounds that this was simply a coincidence and the problem was caused by something else besides static ARP entries;
raystream, nichky, LetMeRepair, proximus, Cha0s, 3bs, Vlad2, sterod, mserge, STEVEUK1, elgrandiegote - We can not seem to reproduce the problem with Winbox login. Can you provide more details? From which version did you upgrade your router? Do you, for example, use RADIUS for Winbox authorisation?
SimWhite, nuffrespect, w0lt, snake27, Hyperlight - Please try to add a new firewall rule at every end of the tunnel and see if it starts to work properly? The rule should be located at the top (at least before drop rules) of input firewall filter rules chain (/ip firewall filter add chain=input action=accept protocol=gre src-address=[address that is configured as a remote-address on your GRE tunnel interface]);
rifkytech, bleblas, marcperea, mducharme, nerxu, jwilkinson6028 - If you cannot login into your router by using API please make sure that you have updated API authentication script (
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login);
anav - Is this problem related to RouterOS v6.45.1 or this is simply a configuration related question?
OndrejHolas - We will resolve this problem as soon as possible;
markos222 - Currently fix is available only in v6.45. Fix will be backported to long-term versions aswell;
adonato - MIPS and MMIPS are two differnet architectures. Is it RB750 or RB750Gr3? Please name precise model.
Hello I have a RouterBOARD 750G r3
uptime: 14h59m39s
version: 6.44.3 (stable)
build-time: Apr/23/2019 12:37:03
factory-software: 6.36.1
free-memory: 167.8MiB
total-memory: 256.0MiB
cpu: MIPS 1004Kc V2.15
cpu-count: 4
cpu-frequency: 880MHz
cpu-load: 6%
free-hdd-space: 172.0KiB
total-hdd-space: 16.3MiB
write-sect-since-reboot: 146662
write-sect-total: 84183238
bad-blocks: 0%
architecture-name: mmips
board-name: hEX
platform: MikroTik
Sorry, bu Does anyone know what to do??
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:14 pm
by fmoses
After upgrading to 6.45.1 PPPOE Profile bandwidth defaults are not creating simple queues. Radius auth is working but if the radius server does not send Mikrotik-Rate for a user ( meaning use the profiles default settings ) it does not. Only users with a defined Mikrotik-Rate get simple queues created... IE for higher bandwidth packages..
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:22 pm
by gdemtcev
RouterOS version 6.45.1 (2019-Jun-27 10:23) has broken RADIUS PAP auth!!!
We have 500+ clients with Mikrotik devices and 27 june in our RADIUS server we see many errors from Mikrotik devices:
Mon Jul 1 11:04:53 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-FA-92-17-09/XX-XX-FA-92-17-0] (from client internet-network port 2152726528 cli XX:XX::FA:92:17:09)
Mon Jul 1 11:12:29 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-80-DC-6F-96/XX-XX-80-DC-6F-9L1\313\033\\ݍ\351\037\231,\205\201҅\236] (from client internet-network port 2152726529 cli XX:XX::80:DC:6F:96)
Mon Jul 1 11:12:40 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-80-DC-6F-96/XX-XX-80-DC-6F-9\006o\377\255\202[\224>\264\351\3103%xe\234] (from client internet-network port 2152726530 cli XX:XX:80:DC:6F:96)
... and man many many logs ...
After update to 6.45.1 all request from Mikrotik to RADIUS have broken last symbol in password (PAP, plain text)
We reproduce this bug in our office on 5+ devices.
How i can open bug report to this error?
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:56 pm
by ivanfm
RouterOS version 6.45.1 (2019-Jun-27 10:23) has broken RADIUS PAP auth!!!
We have 500+ clients with Mikrotik devices and 27 june in our RADIUS server we see many errors from Mikrotik devices:
Mon Jul 1 11:04:53 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-FA-92-17-09/XX-XX-FA-92-17-0] (from client internet-network port 2152726528 cli XX:XX::FA:92:17:09)
Mon Jul 1 11:12:29 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-80-DC-6F-96/XX-XX-80-DC-6F-9L1\313\033\\ݍ\351\037\231,\205\201҅\236] (from client internet-network port 2152726529 cli XX:XX::80:DC:6F:96)
Mon Jul 1 11:12:40 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-80-DC-6F-96/XX-XX-80-DC-6F-9\006o\377\255\202[\224>\264\351\3103%xe\234] (from client internet-network port 2152726530 cli XX:XX:80:DC:6F:96)
... and man many many logs ...
After update to 6.45.1 all request from Mikrotik to RADIUS have broken last symbol in password (PAP, plain text)
We reproduce this bug in our office on 5+ devices.
How i can open bug report to this error?
This reports should be made by e-mail to
support@mikrotik.com .
I have already reported it for hotspot ( #2019070222007151 ) and other person also found same problem in wireless authentication :
viewtopic.php?f=19&t=149811
I did not receive any response from my ticket .
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 10:57 pm
by OndrejHolas
CCR1009, 6.44.3 -> 6.45.1. After upgrade, bonding interface didn't go up. I use two levels of bonding: two low level bonding interfaces, each consisting of two ethernets, bundled to LACP LAG; and one upper level bonding interface, consisting of the two LAGs:
/interface bonding
add mode=802.3ad name=lacp1 slaves=ether5,ether6 transmit-hash-policy=layer-3-and-4
add mode=802.3ad name=lacp2 slaves=ether7,ether8 transmit-hash-policy=layer-3-and-4
add down-delay=1s mode=active-backup name=trunk1 primary=lacp1 slaves=lacp1,lacp2 transmit-hash-policy=layer-2-and-3 up-delay=5s
Up to version 6.44.3 this worked reliably. After upgrade to 6.45.1, the low level bondings (lacp1 and lacp2) go up after boot, but the upper level bonding (trunk1) doesn't notice link change from its slaves and remains down. Disconnecting and reconnecting cables, firmware upgrade, warm and cold reboots, nothing helps.
After disabling and re-enabling upper level bonding interface (/int disa trunk1; /int ena trunk1), it starts to work, including functional failover/failback after link state changes of slaves. Nevertheless, this works only until reboot.
Permanent workaround that worked for me:
/system scheduler
add name="trunk1 fix 6.45.1" on-event=":delay 10s;/int disa trunk1;/int ena trunk1" policy=ftp,reboot,read,write,policy,test,password,sniff,sensitive,romon start-time=startup
Submitted to support as Ticket#2019070222008098.
Ondrej
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:05 pm
by sindy
Sorry, bu Does anyone know what to do??
adonato - instead of the package for mipsbe you've tried to install, download
the package for mmips which is the architecture of your device as reported by
/system resource print.
Re: v6.45.1 [stable] is released!
Posted: Tue Jul 02, 2019 11:11 pm
by gdemtcev
RouterOS version 6.45.1 (2019-Jun-27 10:23) has broken RADIUS PAP auth!!!
We have 500+ clients with Mikrotik devices and 27 june in our RADIUS server we see many errors from Mikrotik devices:
Mon Jul 1 11:04:53 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-FA-92-17-09/XX-XX-FA-92-17-0] (from client internet-network port 2152726528 cli XX:XX::FA:92:17:09)
Mon Jul 1 11:12:29 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-80-DC-6F-96/XX-XX-80-DC-6F-9L1\313\033\\ݍ\351\037\231,\205\201҅\236] (from client internet-network port 2152726529 cli XX:XX::80:DC:6F:96)
Mon Jul 1 11:12:40 2019 : Auth: Login incorrect (rlm_pap: CLEAR TEXT password check failed): [XX-XX-80-DC-6F-96/XX-XX-80-DC-6F-9\006o\377\255\202[\224>\264\351\3103%xe\234] (from client internet-network port 2152726530 cli XX:XX:80:DC:6F:96)
... and man many many logs ...
After update to 6.45.1 all request from Mikrotik to RADIUS have broken last symbol in password (PAP, plain text)
We reproduce this bug in our office on 5+ devices.
How i can open bug report to this error?
This reports should be made by e-mail to
support@mikrotik.com .
I have already reported it for hotspot ( #2019070222007151 ) and other person also found same problem in wireless authentication :
viewtopic.php?f=19&t=149811
I did not receive any response from my ticket .
Already send, twice, but not response yet...(
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 12:59 am
by Panbambaryla
Upgraded RB4011 from 6.44.3 to 6.45.1 - no issues
Well, actually there is one - the bridge MAC address has changed so the network discovery on Windows must be done again. In my case the bridge MAC addr is the same as for eth7 interface. Interesting what it depends on...
Best
Bam
Well, the bridge MAC address changes with RB4011 WiFI reboot so from time to time you will have to change your Windows network from public to private until it cycles all MAC addresses from your eth interfaces. Mikrotik, could you please explain if it is expected behaviour or rather some side effect of the latest firmware?
Best, Bam
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 4:16 am
by Spirch
wow 4 pages already, i'm happy to always wait a few days before installing things that can bring down my network or make thing difficult.
people still deploy stuff in mass without testing them?
time to wait a little bit longer and see the evolution of this thread
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 5:07 am
by Xymox
Upgraded RB4011 from 6.44.3 to 6.45.1 - no issues
Well, actually there is one - the bridge MAC address has changed so the network discovery on Windows must be done again. In my case the bridge MAC addr is the same as for eth7 interface. Interesting what it depends on...
Best
Bam
Well, the bridge MAC address changes with RB4011 WiFI reboot so from time to time you will have to change your Windows network from public to private until it cycles all MAC addresses from your eth interfaces. Mikrotik, could you please explain if it is expected behaviour or rather some side effect of the latest firmware?
Best, Bam
I saw some real weirdness with the 4011.. Maybe the above is part of it. Briefly it was rebooting too. The unit has settled down and I am going to try and downgrade it back to 44.3..
Im running 45.1 on my home CCR and so far it seems fine, but, im just doing a home NAT setup, nothing involved at all.
YEA... Remember everybody, use partitions if your device supports them. Makes for a easy switch back. Before upgrading, copy to and save to a partition. THEN upgrade. You then have a fall back. I would like to be able to pick partitions from the LCD on units that have a LCD..
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 7:51 am
by strods
spacex - We will look into this problem;
Anumrak - Yes, hAP lite and similar routers are designed to run RouterOS bundle package and can be upgraded without any problems, as long as you do not store anything else on your router that might fill up the storage. If there is not enough space on the disk for upgrades - remove files, limit features that use disk and use separate packages instead of RouterOS bundle package;
boquepasha - Which RouterOS version is installed on the router from which you start MAC Telnet session? Is it at least RouterOS version 6.43?
elgrandiegote, enzain, jsadler, kadety - As mentioned in previous posts, we have already resolved this problem and will release Winbox 3.19 with a fix as soon as possible;
dakotabcn, artem1, petrb, fmoses, Xymox - I recommend that you provide supout file to
support@mikrotik.com in order to get more information about the problem that you are experiencing;
Gusse - Can you reproduce this problem once more? Actually, sounds that this was simply a coincidence and the problem was caused by something else;
Cha0s - Unfortunately, this problem is not resolved yet;
mserge - I can not tell you precisely when it will be released, but it will happen as soon as possible (hopefully later today);
adonato - You have not replied which router do you have. Provide the output of the command ":put [/system resource get architecture]". It will tell you which architecture packages you must download in order to upgrade your router;
Panbambaryla - That is why you can set static MAC address on the bridge interface. If it is not set, then the bridge will use MAC address of the first interface which is loaded in RouterOS after a reboot;
Everyone - Please note that MikroTik team provide free support for you if you have a software or hardware related problem. Usually, we reply within three business days (sometimes it might take longer). All of the tickets that you have created will be replied to as soon as possible.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 9:34 am
by Murmaider
170 updates and changes and not one BGP improvement...
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 9:59 am
by boquepasha
That might be the problem, strods. The device from where we were trying to mac-telnet our customer had version 6.42.3. We'll upgrade that device and tell you back with our findings.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 10:33 am
by petrb
Supout file was sent to the support. Thanks
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 10:39 am
by NetVicious
Hi!
As I read before on this thread It seems 6.45.1 has some problem with GRE.
I have some Mikrotik RB450G (call they A, B, C, .....) connected to one RB850Gxx2 (call him as master).
"Master" has one PPTP Server binding for each other (A, B, C).
After upgrading all the devices to 6.45.1, A and C cannot connect to "master" within PPTP, but B was working perfectly.
A, B and C had practically the same configuration.
After trying some changes, I did a downgrade on A and C and it's PPP started to work another time without doing any other change.
I did some screenshots of the logs
Log with 6.45.1 (pptp don't connects)
 Log with 6.44.3 (pptp connects correctly)
Log with 6.44.3 (pptp connects correctly)
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:07 am
by pe1chl
As I read before on this thread It seems 6.45.1 has some problem with GRE.
When you
do make the effort of reading the topic first and seeing others with the same problem, why don't you go that tiny step further and read the replies that they got (also from MikroTik) about the cause of this "problem with GRE" and how you can solve it other dan by downgrading?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:10 am
by pe1chl
Upgraded RB4011 from 6.44.3 to 6.45.1 - no issues
Well, actually there is one - the bridge MAC address has changed so the network discovery on Windows must be done again. In my case the bridge MAC addr is the same as for eth7 interface. Interesting what it depends on...
Best
Bam
Well, the bridge MAC address changes with RB4011 WiFI reboot so from time to time you will have to change your Windows network from public to private until it cycles all MAC addresses from your eth interfaces. Mikrotik, could you please explain if it is expected behaviour or rather some side effect of the latest firmware?
Best, Bam
As always, when the MAC address of a bridge is important you should not configure it as "auto mac" but rather set its "admin mac address" manually.
You can just copy and paste the address it has now.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:30 am
by NetVicious
As I read before on this thread It seems 6.45.1 has some problem with GRE.
When you
do make the effort of reading the topic first and seeing others with the same problem, why don't you go that tiny step further and read the replies that they got (also from MikroTik) about the cause of this "problem with GRE" and how you can solve it other dan by downgrading?
Sorry. I did the downgrade as a fast attempt to fix the problem because I had users waiting to connect.
I read the thread after the downgrade.
I will try the temporal fix later when users are not working.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:39 am
by Anumrak
spacex - We will look into this problem;
Anumrak - Yes, hAP lite and similar routers are designed to run RouterOS bundle package and can be upgraded without any problems, as long as you do not store anything else on your router that might fill up the storage. If there is not enough space on the disk for upgrades - remove files, limit features that use disk and use separate packages instead of RouterOS bundle package;
boquepasha - Which RouterOS version is installed on the router from which you start MAC Telnet session? Is it at least RouterOS version 6.43?
elgrandiegote, enzain, jsadler, kadety - As mentioned in previous posts, we have already resolved this problem and will release Winbox 3.19 with a fix as soon as possible;
dakotabcn, artem1, petrb, fmoses, Xymox - I recommend that you provide supout file to
support@mikrotik.com in order to get more information about the problem that you are experiencing;
Gusse - Can you reproduce this problem once more? Actually, sounds that this was simply a coincidence and the problem was caused by something else;
Cha0s - Unfortunately, this problem is not resolved yet;
mserge - I can not tell you precisely when it will be released, but it will happen as soon as possible (hopefully later today);
adonato - You have not replied which router do you have. Provide the output of the command ":put [/system resource get architecture]". It will tell you which architecture packages you must download in order to upgrade your router;
Panbambaryla - That is why you can set static MAC address on the bridge interface. If it is not set, then the bridge will use MAC address of the first interface which is loaded in RouterOS after a reboot;
Everyone - Please note that MikroTik team provide free support for you if you have a software or hardware related problem. Usually, we reply within three business days (sometimes it might take longer). All of the tickets that you have created will be replied to as soon as possible.
There are no files on the flash drive. Why I didn't need to remove other packages in previous upgrades?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:40 am
by andriys
I will try the temporal fix later when users are not working.
Temporary? Please read the topic once again,
carefully. This version fixes a bug that allowed GRE to work even when
your device was configured improperly. So you do not need to apply a temporary fix, but rather
permanently fix
your configuration.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 12:11 pm
by NetVicious
@andriys. Sorry but I don't saw the official strods post answering a lot of posts of this threads with the info about GRE.
I said temporary fix because I have some RB450G with 6.45.1 running perfectly against a RB850Gx2 with 6.45.1 without any new firewall rule about GRE. That's why I though it's a temporary fix.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 12:20 pm
by jetzcezt
Hello good People :) ,
if you are using PEAR2_Net_RouterOS-1.0.0b6 API by Vasil Rangelov (boenrobot), replace code on Client.php for 7 rows, start at line 292 until line 298, to be :
$request->setArgument('password',$password);
just that one line for make it usable again.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 12:48 pm
by strods
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 12:51 pm
by andriys
@andriys. Sorry but I don't saw the official strods post answering a lot of posts of this threads with the info about GRE.
It was in a (rather long) post
here.
And then a followup
here.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 12:56 pm
by joserudi
After upgrading to 6.45.1 PPPOE Profile bandwidth defaults are not creating simple queues. Radius auth is working but if the radius server does not send Mikrotik-Rate for a user ( meaning use the profiles default settings ) it does not. Only users with a defined Mikrotik-Rate get simple queues created... IE for higher bandwidth packages..
I have the same problem, PPPOE and HOTSPOT Profile defaults bandwith are not creating simple rules. Only its possible acroos radius-rate
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 1:13 pm
by glee
Is there any ETA for long-term release which will fix vulnerabilities?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 1:39 pm
by sindy
@andriys. Sorry but I don't saw the official strods post answering a lot of posts of this threads with the info about GRE.
I said temporary fix because I have some RB450G with 6.45.1 running perfectly against a RB850Gx2 with 6.45.1 without any new firewall rule about GRE. That's why I though it's a temporary fix.
For these GRE (and EoIP, it's the same story as EoIP is an application using GRE) tunnels which work in 6.45.1 without modification, something at both ends must be sending initial connection requests to the tunnel (TCP SYN, DNS queries, whatever), so each end creates an established connection in its local firewall on its own. It may also be caused by keepalives configured on GRE itself if there is no spontaneous traffic. Tunnel ends where keepalive is disabled and all local side devices are just listening servers will not establish the GRE tunnel without the rule in chain input of ip firewall filter (if they are tunnel endponi devices themselves); for transit PPTP, and maybe also for locally terminated PPTP, the PPTP helper must be enabled in ip firewall service-port.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 1:43 pm
by notToNew
Is there any ETA for long-term release which will fix vulnerabilities?
You didnt read the thread, did you?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 2:08 pm
by glee
Is there any ETA for long-term release which will fix vulnerabilities?
You didnt read the thread, did you?
I did, so far there has been only "as soon as possible". It's been 6 days!
I don't get it why it is taking so long.. Fixes for CVE-2018-14847 were released for all channels at same day.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 2:14 pm
by sch
Is there any ETA for long-term release which will fix vulnerabilities?
You didnt read the thread, did you?
I did, so far there has been only "as soon as possible". It's been 3 days!
I don't get it why it is taking so long.. Fixes for CVE-2018-14847 were released for all channels at same day.
Long term: When a Stable release has been out for a while and seems to be stable enough, it gets promoted into the Long Term branch, replacing an older release, which is then moved to Archive. This consecutively adds new features.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 2:23 pm
by jamesw
We are also facing the same issue with Hotspot / RADIUS authentication broken because the Password that is send to RADIUS is garbage/corrupt.
This is affecting 1000+ customers to a big issue.
Case raised; ticket #2019070322005393
Thanks for any help.
James
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 2:31 pm
by pe1chl
Is there any ETA for long-term release which will fix vulnerabilities?
You can fix the vulnerabilities using a firewall rule...
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 2:32 pm
by LeftyTs
In a CRS326, RoS complains about collisions in a half duplex interface. I have had problems before with this interface as it needed to be reset every few days [Ticket#2018122022004844]. I have even set the specific Ethernet interface to "full-duplex=no speed=10Mbps" and those warning messages should not exist as it is normal for collisions to occur in half duplex interfaces.
12:40:19 interface,warning ether16 excessive or late collision, link duplex mismatch?
In any case, there seems to be improvement from previous versions as the Gigabit interfaces have not stopped from working yet when I was testing the beta version.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 2:36 pm
by glee
Is there any ETA for long-term release which will fix vulnerabilities?
You didnt read the thread, did you?
I did, so far there has been only "as soon as possible". It's been 6 days!
I don't get it why it is taking so long.. Fixes for CVE-2018-14847 were released for all channels at same day.
Long term: When a Stable release has been out for a while and seems to be stable enough, it gets promoted into the Long Term branch, replacing an older release, which is then moved to Archive. This consecutively adds new features.
I would argue that releasing software that includes security fixes should be also released to all channels at same day since this will leave devices who are running on long-term channel exploitable. There wasn't even "Testing" channel release, so they really rushed it out only for Stable channel... why? I guess cause of the security fixes.. why not handle long-term same way?
Anywho I upgraded our lab two days ago to 6.45.1. These are my notes:
These models have been running OK.
- RB M33G with R11e-LTE and R11e-4G
Features tested with this release in lab.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 3:23 pm
by pe1chl
I would argue that releasing software that includes security fixes should be also released to all channels at same day since this will leave devices who are running on long-term channel exploitable.
The portion of devices running the latest long-term version and being actively managed by someone/some team who would install a security update in the current long-term channel immediately once it becomes available is likely very, very, very small.
Especially as there is no automatic update mechanism (with its associated security fix channel) in RouterOS, most devices are not regularly updated and many run versions that are very old and have really critical vulnerabilities (compared to this one).
People that elect to run the long-term version also usually are quite conservative in updating it.
Furthermore, you can fix this one with a firewall rule. I have done so early on, and it has not yet revealed attempts to exploit it.
Of course that does not mean it will never happen.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 3:29 pm
by glee
I would argue that releasing software that includes security fixes should be also released to all channels at same day since this will leave devices who are running on long-term channel exploitable.
The portion of devices running the latest long-term version and being actively managed by someone/some team who would install a security update in the current long-term channel immediately once it becomes available is likely very, very, very small.
Especially as there is no automatic update mechanism (with its associated security fix channel) in RouterOS, most devices are not regularly updated and many run versions that are very old and have really critical vulnerabilities (compared to this one).
People that elect to run the long-term version also usually are quite conservative in updating it.
Furthermore, you can fix this one with a firewall rule. I have done so early on, and it has not yet revealed attempts to exploit it.
Of course that does not mean it will never happen.
We are running long-term for customers and we are automatically updating the devices via Ansible with three phases (1day; 5days; 10days delay). Few of our partners are doing the same.
Yes I know we can fix this with firewall rule, we just finished testing our Ansible playbooks for phase1 clients - ~300 devices OK. Going to deploy it to phase2 and phase3 rings now.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 3:34 pm
by seregaelcin
After update 6.44.3->6.45.1 pptp-client doesn't work - connecting.... disconnecting....connecting.... disconnecting....
After downgrade 6.45.1->6.44.3 it works
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 3:36 pm
by Ulypka
2018101022007579 still present
2019.07.03-10:17:52.91@10: 2300: recalculate OSPFv2 routes
2019.07.03-10:17:53.73@10: repairDelete: done, deleted 0
2019.07.03-10:17:53.74@10: repairAdd: done, added 4060
2019.07.03-10:17:54.90@10: 2302: recalculate OSPFv2 routes
2019.07.03-10:25:41.17@3:
2019.07.03-10:25:41.17@3:
2019.07.03-10:25:41.17@3: /nova/bin/route
2019.07.03-10:25:41.17@3: --- signal=12 --------------------------------------------
2019.07.03-10:25:41.17@3:
2019.07.03-10:25:41.17@3: r00=0x000000007fbef774 r01=0x000000007fbef77c r02=0x000000007fbef77c
2019.07.03-10:25:41.17@3: r03=0x000000007fbef848 r04=0x00000000002aeca8 r05=0x00000000003b9940
2019.07.03-10:25:41.17@3: r06=0x0000000000000000 r07=0x0000000000000000 r08=0x0000000000000000
2019.07.03-10:25:41.17@3: r09=0x0000000000000000 r10=0x00000000003b9958 r11=0x00000000003b995c
2019.07.03-10:25:41.17@3: r12=0x000000000057f5f0 r13=0x0000000000000000 r14=0x000000000057f5e8
2019.07.03-10:25:41.17@3: r15=0x0000000000000001 r16=0x0000000000000001 r17=0x00000000002aedcc
2019.07.03-10:25:41.17@3: r18=0x0000000000000001 r19=0x0000000000000000 r20=0x00000000005979e8
2019.07.03-10:25:41.17@3: r21=0x00000000ffffffff r22=0x0000000008ff0003 r23=0x00000000005979d8
2019.07.03-10:25:41.17@3: r24=0x000000007fbef728 r25=0x000000007fbef728 r26=0x00000000000197a0
2019.07.03-10:25:41.17@3: r27=0x0000000000250128 r28=0x0000000077d5b5f0 r29=0x0000000000000100
2019.07.03-10:25:41.17@3: r30=0x000000007fbef780 r31=0x000000007fbef77c r32=0x000000007fbef774
2019.07.03-10:25:41.17@3: r33=0x000000007fbef83c r34=0x000000007fbef848 r35=0x00000000003b9950
2019.07.03-10:25:41.17@3: r36=0x000000007fbef844 r37=0x00000000003b9954 r38=0x00000000002aeca8
2019.07.03-10:25:41.17@3: r39=0x00000000003b9940 r40=0x00000000003c60d8 r41=0x00000000000000fe
2019.07.03-10:25:41.17@3: r42=0x00000000003b9958 r43=0x00000000ac1a1005 r44=0x0000000000000001
2019.07.03-10:25:41.17@3: r45=0x0000000000028948 r46=0x00000000000288c8 r47=0x0000000000000086
2019.07.03-10:25:41.17@3: r48=0x0000000077ae1444 r49=0x00000000000653e0 r50=0x0000000077e5cd70
2019.07.03-10:25:41.17@3: r51=0x0000000077ec2040 r52=0x000000007fbefd90 tp=0x0000000077f22fa0
2019.07.03-10:25:41.17@3: sp=0x000000007fbef760 lr=0x00000000001726b0 pc=0x0000000077d5b618
2019.07.03-10:25:41.17@3: ics=0x0000000000000000 faultnum=0x000000000000001d
2019.07.03-10:25:41.17@3:
2019.07.03-10:25:41.17@3: maps:
2019.07.03-10:25:41.17@3: 00010000-00250000 r-xp 00000000 00:0f 659 /nova/bin/route
2019.07.03-10:25:41.17@3: 77af0000-77b20000 r-xp 00000000 00:0f 468 /lib/libgcc_s.so.1
2019.07.03-10:25:41.17@3: 77b30000-77d30000 r-xp 00000000 00:0f 465 /lib/libc-2.17.so
2019.07.03-10:25:41.17@3: 77d50000-77d70000 r-xp 00000000 00:0f 448 /lib/libuc++.so
2019.07.03-10:25:41.17@3: 77d80000-77da0000 r-xp 00000000 00:0f 451 /lib/libucrypto.so
2019.07.03-10:25:41.17@3: 77db0000-77dc0000 r-xp 00000000 00:0f 453 /lib/libufiber.so
2019.07.03-10:25:41.17@3: 77dd0000-77de0000 r-xp 00000000 00:0f 467 /lib/libdl-2.17.so
2019.07.03-10:25:41.17@3: 77e00000-77e10000 r-xp 00000000 00:0f 454 /lib/libubox.so
2019.07.03-10:25:41.17@3: 77e20000-77ec0000 r-xp 00000000 00:0f 450 /lib/libumsg.so
2019.07.03-10:25:41.17@3: 77ed0000-77f10000 r-xp 00000000 00:0f 462 /lib/ld-2.17.so
2019.07.03-10:25:41.17@3:
2019.07.03-10:25:41.17@3: stack: 0x7fbf0000 - 0x7fbef760
2019.07.03-10:25:41.17@3: 98 26 17 00 00 00 00 00 20 f8 be 7f 00 00 00 00 44 14 ae 77 58 99 3b 00 58 99 3b 00 80 f7 be 7f
2019.07.03-10:25:41.17@3: 00 00 00 00 00 00 00 00 01 00 00 00 05 10 1a ac 05 10 1a ac 00 00 00 00 cc f8 be 7f 00 00 00 00
2019.07.03-10:25:41.17@3:
2019.07.03-10:25:41.17@3: backtrace: 0x77e53ce0 0x77b08e28 0x77d5b618 0x001726b0 0x00172fd0 0x77e5cee0 0x77e56968 0x77e5b3b8 0x77db8170 0x77e59fd0 0x77e51b10 0x77e51be0 0x77e5eda8 0x0001dca0 0x77b4aa40 0x000215a8
2019.07.03-10:25:41.17@3: extra 0x7fbef96c
2019.07.03-10:25:41.17@3: virtual void nv::Looper::dispatchMessage(nv::message&)
2019.07.03-10:25:41.17@3: Handler: 0x00000081
2019.07.03-10:25:41.17@3: true--- nv::message --------
2019.07.03-10:25:41.17@3: bool [local::1002]=true
2019.07.03-10:25:41.17@3: bool [SYS_REPLYEXP]=true
2019.07.03-10:25:41.17@3: u32 [SYS_POLICY]=-16385 0xffffbfff 255.191.255.255
2019.07.03-10:25:41.17@3: u32 [STD_FILTER]=5 0x5 5.0.0.0
2019.07.03-10:25:41.17@3: u32 [SYS_TYPE]=TYPE_REQUEST
2019.07.03-10:25:41.17@3: u32 [STD_GETALLID]=6162984 0x5e0a28 40.10.94.0
2019.07.03-10:25:41.17@3: u32 [SYS_REQID]=556 0x22c 44.2.0.0
2019.07.03-10:25:41.17@3: u32 [SYS_CMD]=CMD_GETALL
2019.07.03-10:25:41.17@3: message [STD_GETALL_COOKIE]...
2019.07.03-10:25:41.17@3: true --- nv::message --------
2019.07.03-10:25:41.17@3: u32 [3]=-1407578107 0xac1a1005 5.16.26.172
2019.07.03-10:25:41.17@3: u32 [STD_ID]=1 0x1 1.0.0.0
2019.07.03-10:25:41.17@3: u32 [1]=1 0x1 1.0.0.0
2019.07.03-10:25:41.17@3: u32 [2]=-1407578107 0xac1a1005 5.16.26.172
2019.07.03-10:25:41.17@3: u32 [14]=2824504 0x2b1938 56.25.43.0
2019.07.03-10:25:41.17@3: u32[0x00000000] [SYS_TO]=
2019.07.03-10:25:41.17@3: u32[0x00000002] [SYS_FROM]=0x00000030, 0x000000
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 5:05 pm
by seregaelcin
After update 6.44.3->6.45.1 pptp-client doesn't work - connecting.... disconnecting....connecting.... disconnecting....
After downgrade 6.45.1->6.44.3 it works
i created gre input firewall rule and replaced over fasstrack. pptp-client connected. Solved
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 5:20 pm
by Panbambaryla
After update 6.44.3->6.45.1 pptp-client doesn't work - connecting.... disconnecting....connecting.... disconnecting....
After downgrade 6.45.1->6.44.3 it works
i created gre input firewall rule and replaced over fasstrack. pptp-client connected. Solved
No need to...
Just enable ip firewall service ports pptp NAT helper... It's been mentioned so many timees in here...
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 5:33 pm
by maxsaf
The Dude - RouterOS checkmark doesn't work anymore. Error "invalid user name or password (6), next attempt at Jul/04 14:25:10"
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 6:04 pm
by gepelbaum
My update report:
Dear, after updating the 6.44.3 version 6.45.1 experience that the name field of the ipsec tunnels was removed, this occurred in all devices where I had ipsec configured and in some had several tunnels configured.
For the rest, I did not see any problem although this if I present productivity problems in the clients.
regards
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 6:30 pm
by nmt1900
It looks like SNMP access from Dude works OK with SNMPv1 or SNMPv2c. Maybe something with SNMPv3 authentication or encryption is wrong in Dude?
It looks like Dude has problems with SNMP access.
snmpwalk to other Mikrotik device causes this to appear in log of target device
10:22:24 snmp,debug unsupported v3 security level
10:22:24 snmp,debug v3 err: 0 unsupported security
10:22:24 snmp,debug bad packet
and snmpwalk times out. We have LibreNMS set up for monitoring and
it works fine as it did before.SNMP is set up as v3 private access.
Dude is updated to 6.45.1. It is hard to say whether Dude is the problem or RouterOS on the device itself...
I have that same problem
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 6:40 pm
by mserge
I tried it but i still get same error "Wrong user or password", any ideas?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 6:41 pm
by theplanet
There is a major problem with Hotspot + Radius + Mac Authentication... i have dmasoftlab radius and after the upgrade no client connected automatically... before the upgrade all working... and now no mac auth... I've found the problem, is is http pap , has to be disabled.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 7:43 pm
by nostromog
I upgraded 2 mAP Lite without a single issue, and another old 750GL. Same
On the other side, the hAP ac that could not be upgraded/downgraded to 6.44.* or 6.45beta* because it had the 100% looping CPU on ipsec is stil behaving the same.
It hangs in some initial script that tries to modify ipsec policies depending on dynamic local ip, it hangs on "/ export" or "/ip ipsec <whatever>". I can't generate a supout because it hangs

Again, downgrading to long-term works, and it recovers a very simple and working, ipsec configuration:
/ip ipsec export hide-sensitive
# jul/03/2019 18:35:52 by RouterOS 6.43.16
# software id = <edited>
#
# model = RouterBOARD 962UiGS-5HacT2HnT
# serial number = <edited>
/ip ipsec mode-config
add address-pool=vpn2 name=RW-cfg split-include=192.168.87.0/24,192.168.90.0/24,192.168.91.0/24
/ip ipsec policy group
add name=RoadWarrior
/ip ipsec peer
add auth-method=pre-shared-key-xauth generate-policy=port-strict mode-config=RW-cfg passive=yes policy-template-group=RoadWarrior
/ip ipsec policy
add dst-address=192.168.91.0/24 group=RoadWarrior src-address=192.168.87.0/24 template=yes
add dst-address=192.168.91.0/24 group=RoadWarrior src-address=192.168.90.0/24 template=yes
add dst-address=192.168.91.0/24 group=RoadWarrior src-address=192.168.91.0/24 template=yes
add disabled=yes dst-address=192.168.91.0/24 group=RoadWarrior src-address=0.0.0.0/0 template=yes
/ip ipsec user
add name=user2
add name=user
add name=user3
Deleting the ipsec configuration and upgrading loops the same. I'll keep it in long-term until either a stable version works or a long-term version works "past" the problem, or I can make netinstall work, which I have not been able for the moment...
There is another, remote office machine, that I'm scared to upgrade because I'm afraid that the issue will happen again and I can't easily recover the machine. It is quite critical and far away.
Is any of the other people that was experiencing with me this 100% CPU loop in ipsec in 6.44-6.45 been able to recover? How?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 8:43 pm
by sindy
It hangs in some initial script that tries to modify ipsec policies depending on dynamic local ip, it hangs on "/ export" or "/ip ipsec <whatever>". I can't generate a supout because it hangs

Have you tried to reset the machine to defaults before or better after upgrade to 6.45.1 and then manually create the IPsec configuration from the export rather than letting the upgrade script do that? This clearly cannot be used on the production machine but it should at least confirm that the IPsec part is the trigger, so you could be able to remove the IPsec configuration on the production machine before the upgrade if you can provide some other means to access it remotely (ssh, https) and recreate the IPsec part after the upgrade.
Other than that, a support.rif of the state before upgrade should be enough for support to simulate the same process at their end.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 9:52 pm
by owsugde
All I can say is be very careful with this update. I have rolled it out on some remote devices, and now, one isn't having ethernet connectivity at all (at the least) and the other isn't coming back up over OVPN.
Can't say more about what has caused this in particular, yet. Probably will have to be on premises tomorrow because of this, more on it then...
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 10:33 pm
by DotTest37
What does exactly mean:
!) user - removed insecure password storage;
?
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 10:37 pm
by pe1chl
What does exactly mean:
!) user - removed insecure password storage;
?
It is already written in the head of the release notes!
In older RouterOS versions before 6.43 the passwords were stored in plaintext.
In the 6.43 version they were changed to hashes but the plaintext version remained so you could downgrade and still have your passwords.
Now the plaintext versions are deleted, so when you downgrade from 6.45.1 to a 6.42 or older version you lose all your passwords.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 10:54 pm
by dlausch
i have found the failure.
connecting with the android app over vpn (i am not at home) is fine.
connecting with winbox from my windows laptop over vpn is fone too.
only winbox running with wine on my macbook shows this failure
and after deleting the cache in winbox it connects again on my macbook
I've got a similar issue...
I'm unable to connect my Router / APs etc by IOS app, no matter if VPN or WLAN.
The logs say: "system,error,critical login failure for user david from 10.200.5.13 via tikapp"
Via Winbox, SSH or Web no problems.
So I had to turn of the network for my Kids by ssh, not by app...
Greetz
David
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:08 pm
by CharlyBrown
Hi Guys, I recently updated 2 of my routers, one of them has Dude installed, and when I try to login through API, I receive the same error.
The las version installed on my routers are 6.44, and the API login style is the one indicated on the wiki.
Other strange thing, when I try to use AUTO UPGRADE option from other routers I receive the same error. (wrong password). The configured server with update packages are the router with DUDE, with 6.51 version.-
I try to reset de admin password, api password and nothing happened.
When I try to connect through API and AUTO UPGRADE option between routers with 6.44 version, everything works fine.
If need more information about those tests please tell me.
Re: v6.45.1 [stable] is released!
Posted: Wed Jul 03, 2019 11:12 pm
by DotTest37
What does exactly mean:
!) user - removed insecure password storage;
?
It is already written in the head of the release notes!
In older RouterOS versions before 6.43 the passwords were stored in plaintext.
In the 6.43 version they were changed to hashes but the plaintext version remained so you could downgrade and still have your passwords.
Now the plaintext versions are deleted, so when you downgrade from 6.45.1 to a 6.42 or older version you lose all your passwords.
Which passwords?
The one used to log in on Router OS?
The ones for PPP accounts?
Anything else?
Which ones?
Are we talking also the password visibility when you do EXPORT on the CLI? (you see all passwords there)
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 1:51 am
by salah
can anyone help me to enable this future (dot1x) on my LAN network
I have a tp-link access point with WPA/WPA2 enterprise authentication.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 2:31 am
by faraujo88
Hi Guys
I am having problem to update my device,
it complete and reboot , but when i go to check the currentversion, is still 6.42 and not 6.45
Please Help
Can U send log? did u check correct architecture?
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 2:32 am
by faraujo88
What does exactly mean:
!) user - removed insecure password storage;
?
It is already written in the head of the release notes!
In older RouterOS versions before 6.43 the passwords were stored in plaintext.
In the 6.43 version they were changed to hashes but the plaintext version remained so you could downgrade and still have your passwords.
Now the plaintext versions are deleted, so when you downgrade from 6.45.1 to a 6.42 or older version you lose all your passwords.
Which passwords?
The one used to log in on Router OS?
The ones for PPP accounts?
Anything else?
Which ones?
Are we talking also the password visibility when you do EXPORT on the CLI? (you see all passwords there)
I guess it refears to Management users.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 5:59 am
by winet
i think, v6.45.1 still have security hole. this happened last night. it's v6.45.1, and had already created new user credential on it, removed the old one. and somehow, the router made a vpn interface with the old deleted user login.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 6:19 am
by xtrans
This version is not automatically show captive portal on hotspot
I downgrade to 6.44.3 and fix.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 6:35 am
by winet
ah got it, there is something on the system scheduler
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 7:05 am
by strods
joserudi - Please send supout file to
support@mikrotik.com. Generate file while the problem is present and name at least single user which does not get rate-limit;
LeftyTs, Ulypka, gepelbaum, nostromog, CharlyBrown, xtrans - Please send supout file to
support@mikrotik.com. Generate file while the problem is present;
mserge - Make sure that you use Winbox 3.19. If the problem persists, then generate a new supout file on your router after failed Winbox login attempt and send it to
support@mikrotik.com;
owsugde - Is it possible that you are using a certificate verification feature which was introduced in this release? "ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066)"
dlausch - Sound like you have the same problem as we did with Winbox. Also new iOS MikroTik mobile application update will be released very soon;
Everyone - Everyone who is experiencing RADIUS related problems with authentication since v6.45, we will soon release 6.46beta version with potential fix for the problem;
Everyone - Long-term version will be released as soon as possible. There is no ETA since everyone will want version as stable as possible. We can not simply name date and time when the version will be released. It depends on test results.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 7:32 am
by xtrans
Requesting for /ip hotspot active Session time left to be editable.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 7:49 am
by bubniakz
we use CRM, ISPadmin, which communicates with MKT by API, but when updating to 6.45.1
API doesnt work, because new API authentification is not implement in our CRM. It says
"killing PID 25009, API number exceeds the limit", but when downgrade to 6.44.3, which
worked with CRM prior and should have compatibility with old API authentification, it
doesnt work anymore and still have API error.
Log in MKT: "login failure via API"
thanks for help
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 8:30 am
by buset1974
joserudi - Please send supout file to
support@mikrotik.com. Generate file while the problem is present and name at least single user which does not get rate-limit;
LeftyTs, Ulypka, gepelbaum, nostromog, CharlyBrown, xtrans - Please send supout file to
support@mikrotik.com. Generate file while the problem is present;
mserge - Make sure that you use Winbox 3.19. If the problem persists, then generate a new supout file on your router after failed Winbox login attempt and send it to
support@mikrotik.com;
owsugde - Is it possible that you are using a certificate verification feature which was introduced in this release? "ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066)"
dlausch - Sound like you have the same problem as we did with Winbox. Also new iOS MikroTik mobile application update will be released very soon;
Everyone - Everyone who is experiencing RADIUS related problems with authentication since v6.45, we will soon release 6.46beta version with potential fix for the problem;
Everyone - Long-term version will be released as soon as possible. There is no ETA since everyone will want version as stable as possible. We can not simply name date and time when the version will be released. It depends on test results.
CCR1036-8G-2S+ , having random reboot by watchdog after upgrade to 6.45.1.
I have sent the supout file
thx
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 8:42 am
by tesme33
Hi
im attaching the config. There is nothing fancy in. But once the package is downloaded only 60KiB are left on the flash.
And this is just not enough. Now i need to figure out how to upgrade ind. packages step by step. Never did this before.
In between i was upgrading a CCR1009. Works. But also no fancy config. Just routing,dhcp and firewall.
Hi
upgraded crs326 and one hap lite without issues : 6.43.3 --> 6.45.1
one hap lite wont upgrade. I suspect space problem, but there are no files on the system.
It's the oroblem with free memory. Devices with small flash (less than 64MB) download upgrade packages to RAM ... and for that some 12MB RAM should be free. Free RAM on your hAP lite is quite low ... do you have some large address list?
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 8:56 am
by arsalansiddiqui
Hi, i have upgraded my two RB750 to v6.45.1 and they are not let me access through api, and my 6.43.8, 6.44.3 is connecting to api normally, i'm using default port and i'm accessing in php.
Before upgrading i can connect both tiks with api.
Thanks
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 9:14 am
by kanitelka
After update 6.44.3->6.45.1 pptp-client doesn't work - connecting.... disconnecting....connecting.... disconnecting....
After downgrade 6.45.1->6.44.3 it works
i created gre input firewall rule and replaced over fasstrack. pptp-client connected. Solved
The problem is only with PPTP?
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 9:15 am
by Reinis
Hi, i have upgraded my two RB750 to v6.45.1 and they are not let me access through api, and my 6.43.8, 6.44.3 is connecting to api normally, i'm using default port and i'm accessing in php.
Before upgrading i can connect both tiks with api.
Thanks
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 10:35 am
by Chupaka
but when downgrade to 6.44.3, which
worked with CRM prior and should have compatibility with old API authentification, it
doesnt work anymore and still have API error.
Log in MKT: "login failure via API"
thanks for help
When you upgraded to 6.45, plaintext passwords were removed. That's why you cannot use old login method on that router. You may try to recreate/reset password for API user on 6.44
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 11:08 am
by mangust479
I updated 37 routers of different models, at all the error is observed: one core of CPU is loaded for 100% by process of routing, OSPF falls off when you come into the OSPF settings that there in general there is nothing. There is information when it is able to be corrected? I wrote to support already.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 11:32 am
by le1
Hello, I have problem with radius server authentication

hotspot,info,debug {MAC Address} (192.168.88.18): login failed: RADIUS server is not responding
hotspot,info,debug {MAC Address} (192.168.88.18): trying to log in by http-pap
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 12:34 pm
by arsalansiddiqui
Hi, i have upgraded my two RB750 to v6.45.1 and they are not let me access through api, and my 6.43.8, 6.44.3 is connecting to api normally, i'm using default port and i'm accessing in php.
Before upgrading i can connect both tiks with api.
Thanks
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login
i did not understand it, what changes should i do to login ?
$API->connect($ip_address, $api_username, $api_password, $port );
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 12:44 pm
by arsalansiddiqui
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 1:02 pm
by mrz
@arsalansiddiqui you need to fix your API wrapper so that login parameters are sent as described in the wiki.
Here is another topic
viewtopic.php?f=9&t=136475
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 1:22 pm
by arsalansiddiqui
@arsalansiddiqui you need to fix your API wrapper so that login parameters are sent as described in the wiki.
Here is another topic
viewtopic.php?f=9&t=136475
I got it

Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 1:35 pm
by tdw
we use CRM, ISPadmin, which communicates with MKT by API, but when updating to 6.45.1
API doesnt work, because new API authentification is not implement in our CRM. It says
"killing PID 25009, API number exceeds the limit", but when downgrade to 6.44.3, which
worked with CRM prior and should have compatibility with old API authentification, it
doesnt work anymore and still have API error.
Log in MKT: "login failure via API"
thanks for help
@bubniakz As stated in the release notes, and as noted here
https://ispadmin.eu/en/mikrotik-api-in- ... t-working/
As 6.45.x erases passwords stored with the 'old' method of reversible encryption, after downgrading you will also have to recreate the password or restore from backup.
When upgrading firmware:
6.42.12 and prior: old method only -> 6.43.x & 6.44.x: old & new methods -> 6.45.x and later: new method only
When downgrading firmware:
6.45.x and later: new method only -> 6.43.x & 6.44.x: new method -> 6.42.12 and prior: no passwords
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 1:57 pm
by TDodger
I've read the thread, I seem to be the only one having problems with WebFig...
Upgraded from 6.44.3 to 6.45.1
WinBox worked/works fine, both 3.18 and 3.19
But when I use WebFig, it works only over http Port 80, not via https Port 443 which I normally use.
It says: ERROR: Not Found
But same user/password works via WinBox and http.
So I guess maybe a problem with my (self created) certificate? I didn't change anything in the config after upgrading to 6.45.1
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 1:57 pm
by nichky
*) dhcpv4-server - added "client-mac-limit" parameter;
which number over here goes?
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 2:06 pm
by owsugde
owsugde - Is it possible that you are using a certificate verification feature which was introduced in this release? "ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066)"
I don't think this is it, because a cold reboot done by the customer "fixed" it. At this time I don't know what it could have been really. For now, I went to longterm anyway, because RADIUS hotspot login by http-pap was disabled on stable somehow and we're using this.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 2:52 pm
by Elans
It looks like Dude has problems with SNMP access.
snmpwalk to other Mikrotik device causes this to appear in log of target device
10:22:24 snmp,debug unsupported v3 security level
10:22:24 snmp,debug v3 err: 0 unsupported security
10:22:24 snmp,debug bad packet
and snmpwalk times out. We have LibreNMS set up for monitoring and
it works fine as it did before.SNMP is set up as v3 private access.
Dude is updated to 6.45.1. It is hard to say whether Dude is the problem or RouterOS on the device itself...
spacex
nmt1900
Make sure that your monitored device "IP-SNMP communities" and The Dude "server settings" SNMP custom profile does not have any mismatch.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 3:01 pm
by pe1chl
we use CRM, ISPadmin, which communicates with MKT by API, but when updating to 6.45.1
API doesnt work, because new API authentification is not implement in our CRM.
You should ask the creator of that software for an update, or investigate how it works and update it yourself.
(e.g. when it uses the wellknown PHP API you can update just that file)
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 3:25 pm
by nmt1900
spacex
nmt1900
Make sure that your monitored device "IP-SNMP communities" and The Dude "server settings" SNMP custom profile does not have any mismatch.
There is no mismatch and these community settings have been used for long time. Only Dude fails and it worked fine with 6.44.3. After testing it looks like only way to get it work with Dude is to use SNMPv2c or SNMPv1.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 3:38 pm
by Ulypka
joserudi - Please send supout file to
support@mikrotik.com. Generate file while the problem is present and name at least single user which does not get rate-limit;
LeftyTs, Ulypka, gepelbaum, nostromog, CharlyBrown, xtrans - Please send supout file to
support@mikrotik.com. Generate file while the problem is present;
mserge - Make sure that you use Winbox 3.19. If the problem persists, then generate a new supout file on your router after failed Winbox login attempt and send it to
support@mikrotik.com;
owsugde - Is it possible that you are using a certificate verification feature which was introduced in this release? "ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066)"
dlausch - Sound like you have the same problem as we did with Winbox. Also new iOS MikroTik mobile application update will be released very soon;
Everyone - Everyone who is experiencing RADIUS related problems with authentication since v6.45, we will soon release 6.46beta version with potential fix for the problem;
Everyone - Long-term version will be released as soon as possible. There is no ETA since everyone will want version as stable as possible. We can not simply name date and time when the version will be released. It depends on test results.
It is exist Ticket:
[Ticket#2018101022007579]
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 5:25 pm
by fdk
Hi,
After upgrading to stable version, I lost access via my users' users even by reconfiguring the passwords. the pppoe server also stopped interpreting the maximum time set by the uptime AAA for the connections. I was forced to go back to version 4.43.16 which normalized.
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 5:51 pm
by llag
yesterday I upgrade the CRS317 and the CRS328 POE. Since the upgrade I have seen 70 flaps of the link between the 2. See also
viewtopic.php?f=2&t=141633&p=738127&hil ... 3d#p738127
I used to see the link flap once a day or every few days on 6.44
Mikrotik, what is happening here?
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 6:41 pm
by machack
RouterOS version 6.45.1 has been released in public "stable" channel!
Before an upgrade:
1) Remember to make backup/export files before an upgrade and save them on another storage device;
2) Make sure the device will not lose power during upgrade process;
3) Device has enough free storage space for all RouterOS packages to be downloaded.
What's new in 6.45.1 (2019-Jun-27 10:23):
Important note!!!
Due to removal of compatibility with old version passwords in this version, downgrading to any version prior to v6.43 (v6.42.12 and older) will clear all user passwords and allow password-less authentication. Please secure your router after downgrading.
Old API authentication method will also no longer work, see documentation for new login procedure:
https://wiki.mikrotik.com/wiki/Manual:API#Initial_login
MAJOR CHANGES IN v6.45.1:
----------------------
!) dot1x - added support for IEEE 802.1X Port-Based Network Access Control;
!) ike2 - added support for EAP authentication methods (eap-tls, eap-ttls, eap-peap, eap-mschapv2) as initiator;
!) security - fixed vulnerabilities CVE-2018-1157, CVE-2018-1158;
!) security - fixed vulnerabilities CVE-2019-11477, CVE-2019-11478, CVE-2019-11479;
!) security - fixed vulnerability CVE-2019-13074;
!) user - removed insecure password storage;
----------------------
Changes in this release:
*) bridge - correctly display bridge FastPath status when vlan-filtering or dhcp-snooping is used;
*) bridge - correctly handle bridge host table;
*) bridge - fixed log message when hardware offloading is being enabled;
*) bridge - improved stability when receiving traffic over USB modem with bridge firewall enabled;
*) capsman - fixed CAP system upgrading process for MMIPS;
*) capsman - fixed interface-list usage in access list;
*) ccr - improved packet processing after overloading interface;
*) certificate - added "key-type" field;
*) certificate - added support for ECDSA certificates (prime256v1, secp384r1, secp521r1);
*) certificate - fixed self signed CA certificate handling by SCEP client;
*) certificate - made RAM the default CRL storage location;
*) certificate - removed DSA (D) flag;
*) certificate - removed "set-ca-passphrase" parameter;
*) chr - legacy adapters require "disable-running-check=yes" to be set;
*) cloud - added "replace" parameter for backup "upload-file" command;
*) conntrack - fixed GRE protocol packet connection-state matching (CVE-2014-8160);
*) conntrack - significant stability and performance improvements;
*) crs317 - fixed known multicast flooding to the CPU;
*) crs3xx - added ethernet tx-drop counter;
*) crs3xx - correctly display auto-negotiation information for SFP/SFP+ interfaces in 1Gbps rate;
*) crs3xx - fixed auto negotiation when 2-pair twisted cable is used (downshift feature);
*) crs3xx - fixed "tx-drop" counter;
*) crs3xx - improved switch-chip resource allocation on CRS326, CRS328, CRS305;
*) defconf - added "custom-script" field that prints custom configuration installed by Netinstall;
*) defconf - automatically set "installation" parameter for outdoor devices;
*) defconf - changed default configuration type to AP for cAP series devices;
*) defconf - fixed channel width selection for RU locked devices;
*) dhcp - create dual stack queue based on limitations specified on DHCPv4 server lease configuration;
*) dhcp - do not require lease and binding to have the same configuration for dual-stack queues;
*) dhcp - show warning in log if lease and binding dual-stack related parameters do not match and create separate queues;
*) dhcpv4-server - added "client-mac-limit" parameter;
*) dhcpv4-server - added IP conflict logging;
*) dhcpv4-server - added RADIUS accounting support with queue based statistics;
*) dhcpv4-server - added "vendor-class-id" matcher (CLI only);
*) dhcpv4-server - improved stability when performing "check-status" command;
*) dhcpv4-server - replaced "busy" lease status with "conflict" and "declined";
*) dhcpv6-client - added option to disable rapid-commit;
*) dhcpv6-client - fixed status update when leaving "bound" state;
*) dhcpv6-server - added additional RADIUS parameters for Prefix delegation, "rate-limit" and "life-time";
*) dhcpv6-server - added "address-list" support for bindings;
*) dhcpv6-server - added "insert-queue-before" and "parent-queue" parameters;
*) dhcpv6-server - added RADIUS accounting support with queue based statistics;
*) dhcpv6-server - added "route-distance" parameter;
*) dhcpv6-server - fixed dynamic IPv6 binding without proper reference to the server;
*) dhcpv6-server - override prefix pool and/or DNS server settings by values received from RADIUS;
*) discovery - correctly create neighbors from VLAN tagged discovery messages;
*) discovery - fixed CDP packets not including address on slave ports (introduced in v6.44);
*) discovery - improved neighbour's MAC address detection;
*) discovery - limit max neighbour count per interface based on total RAM memory;
*) discovery - show neighbors on actual mesh ports;
*) e-mail - include "message-id" identification field in e-mail header;
*) e-mail - properly release e-mail sending session if the server's domain name can not be resolved;
*) ethernet - added support for 25Gbps and 40Gbps rates;
*) ethernet - fixed running (R) flag not present on x86 interfaces and CHR legacy adapters;
*) ethernet - increased loop warning threshold to 5 packets per second;
*) fetch - added SFTP support;
*) fetch - improved user policy lookup;
*) firewall - fixed fragmented packet processing when only RAW firewall is configured;
*) firewall - process packets by firewall when accepted by RAW with disabled connection tracking;
*) gps - fixed missing minus close to zero coordinates in dd format;
*) gps - make sure "direction" parameter is upper case;
*) gps - strip unnecessary trailing characters from "longtitude" and "latitude" values;
*) gps - use "serial0" as default port on LtAP mini;
*) hotspot - added "interface-mac" variable to HTML pages;
*) hotspot - moved "title" HTML tag after "meta" tags;
*) ike1 - adjusted debug packet logging topics;
*) ike2 - added support for ECDSA certificate authentication (rfc4754);
*) ike2 - added support for IKE SA rekeying for initiator;
*) ike2 - do not send "User-Name" attribute to RADIUS server if not provided;
*) ike2 - improved certificate verification when multiple CA certificates received from responder;
*) ike2 - improved child SA rekeying process;
*) ike2 - improved XAuth identity conversion on upgrade;
*) ike2 - prefer SAN instead of DN from certificate for ID payload;
*) ippool - improved logging for IPv6 Pool when prefix is already in use;
*) ipsec - added dynamic comment field for "active-peers" menu inherited from identity;
*) ipsec - added "ph2-total" counter to "active-peers" menu;
*) ipsec - added support for RADIUS accounting for "eap-radius" and "pre-shared-key-xauth" authentication methods;
*) ipsec - added traffic statistics to "active-peers" menu;
*) ipsec - disallow setting "src-address" and "dst-address" for transport mode policies;
*) ipsec - do not allow adding identity to a dynamic peer;
*) ipsec - fixed policies becoming invalid after changing priority;
*) ipsec - general improvements in policy handling;
*) ipsec - properly drop already established tunnel when address change detected;
*) ipsec - renamed "remote-peers" to "active-peers";
*) ipsec - renamed "rsa-signature" authentication method to "digital-signature";
*) ipsec - replaced policy SA address parameters with peer setting;
*) ipsec - use tunnel name for dynamic IPsec peer name;
*) ipv6 - improved system stability when receiving bogus packets;
*) ltap - renamed SIM slots "up" and "down" to "2" and "3";
*) lte - added initial support for Vodafone R216-Z;
*) lte - added passthrough interface subnet selection;
*) lte - added support for manual operator selection;
*) lte - allow setting empty APN;
*) lte - allow to specify URL for firmware upgrade "firmware-file" parameter;
*) lte - do not show error message for info commands that are not supported;
*) lte - fixed session reactivation on R11e-LTE in UMTS mode;
*) lte - improved firmware upgrade process;
*) lte - improved "info" command query;
*) lte - improved R11e-4G modem operation;
*) lte - renamed firmware upgrade "path" command to "firmware-file" (CLI only);
*) lte - show alphanumeric value for operator info;
*) lte - show correct firmware revision after firmware upgrade;
*) lte - use default APN name "internet" when not provided;
*) lte - use secondary DNS for DNS server configuration;
*) m33g - added support for additional Serial Console port on GPIO headers;
*) ospf - added support for link scope opaque LSAs (Type 9) for OSPFv2;
*) ospf - fixed opaque LSA type checking in OSPFv2;
*) ospf - improved "unknown" LSA handling in OSPFv3;
*) ovpn - added "verify-server-certificate" parameter for OVPN client (CVE-2018-10066);
*) ppp - added initial support for Quectel BG96;
*) proxy - increased minimal free RAM that can not be used for proxy services;
*) rb3011 - improved system stability when receiving bogus packets;
*) rb4011 - fixed MAC address duplication between sfp-sfpplus1 and wlan1 interfaces (wlan1 configuration reset required);
*) rb921 - improved system stability ("/system routerboard upgrade" required);
*) routerboard - renamed 'sim' menu to 'modem';
*) sfp - fixed S-35LC20D transceiver DDMI readouts after reboot;
*) sms - added USSD message functionality under "/tool sms" (CLI only);
*) sms - allow specifying multiple "allowed-number" values;
*) sms - improved delivery report logging;
*) snmp - added "dot1dStpPortTable" OID;
*) snmp - added OID for neighbor "interface";
*) snmp - added "write-access" column to community print;
*) snmp - allow setting interface "adminStatus";
*) snmp - fixed "send-trap" not working when "trap-generators" does not contain "temp-exception";
*) snmp - fixed "send-trap" with multiple "trap-targets";
*) snmp - improved reliability on SNMP service packet validation;
*) snmp - properly return multicast and broadcast packet counters for IF-MIB OIDs;
*) ssh - accept remote forwarding requests with empty hostnames;
*) ssh - added new "ssh-exec" command for non-interactive command execution;
*) ssh - fixed non-interactive multiple command execution;
*) ssh - improved remote forwarding handling (introduced in v6.44.3);
*) ssh - improved session rekeying process on exchanged data size threshold;
*) ssh - keep host keys when resetting configuration with "keep-users=yes";
*) ssh - use correct user when "output-to-file" parameter is used;
*) sstp - improved stability when received traffic hits tarpit firewall;
*) supout - added IPv6 ND section to supout file;
*) supout - added "kid-control devices" section to supout file;
*) supout - added "pwr-line" section to supout file;
*) supout - changed IPv6 pool section to output detailed print;
*) switch - properly reapply settings after switch chip reset;
*) tftp - added "max-block-size" parameter under TFTP "settings" menu (CLI only);
*) tile - improved link fault detection on SFP+ ports;
*) tr069-client - added LTE CQI and IMSI parameter support;
*) tr069-client - fixed potential memory corruption;
*) tr069-client - improved error reporting with incorrect firware upgrade XML file;
*) traceroute - improved stability when sending large ping amounts;
*) traffic-generator - improved stability when stopping traffic generator;
*) tunnel - removed "local-address" requirement when "ipsec-secret" is used;
*) userman - added support for "Delegated-IPv6-Pool" and "DNS-Server-IPv6-Address" (CLI only);
*) w60g - do not show unused "dmg" parameter;
*) w60g - prefer AP with strongest signal when multiple APs with same SSID present;
*) w60g - show running frequency under "monitor" command;
*) winbox - added "System/SwOS" menu for all dual-boot devices;
*) winbox - do not allow setting "dns-lookup-interval" to "0";
*) winbox - show "LCD" menu only on boards that have LCD screen;
*) wireless - fixed frequency duplication in the frequency selection menu;
*) wireless - fixed incorrect IP header for RADIUS accounting packet;
*) wireless - improved 160MHz channel width stability on rb4011;
*) wireless - improved DFS radar detection when using non-ETSI regulated country;
*) wireless - improved installation mode selection for wireless outdoor equipment;
*) wireless - set default SSID and supplicant-identity the same as router's identity;
*) wireless - updated "china" regulatory domain information;
*) wireless - updated "new zealand" regulatory domain information;
*) www - improved client-initiated renegotiation within the SSL and TLS protocols (CVE-2011-1473);
What's new in 6.45 (2019-Jun-21 09:00):
(factory only release)
What's new in 6.44.4 (2019-May-09 12:14):
(factory only release)
To upgrade, click "Check for updates" at /system package in your RouterOS configuration interface, or head to our download page:
http://www.mikrotik.com/download
If you experience version related issues, then please send supout file from your router to
support@mikrotik.com. File must be generated while router is not working as suspected or after some problem has appeared on device
Please keep this forum topic strictly related to this particular RouterOS release.
After Upgrade 6.45.1.... My DHCP server dosent work anymore.. use radius to validate.... roolback...
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 7:10 pm
by maxsaf
On my CRS317-1G-16S+ i see in log "timeout while waiting for program 16" and "timeout while waiting for program 20".
Also errors "login failure for user admin from (Dude IP) via dude"
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 8:49 pm
by seregaelcin
No need to...
Just enable ip firewall service ports pptp NAT helper... It's been mentioned so many timees in here...
Thank, i didn't know
Re: v6.45.1 [stable] is released!
Posted: Thu Jul 04, 2019 9:34 pm
by petrb
After Upgrade 6.45.1.... My DHCP server dosent work anymore.. use radius to validate.... roolback...
Fix in 6.46beta
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 7:49 am
by chubbs596
Hi Mikrotik support
I have also send a support email for this.
We make use of the Auto upgrade feature we have the necesary upgrade files hosted on a central router with a user upgrade added for the Auto upgrade purpose
We add the below on all client routers, and with scripts and schedulers we daily check for upgrades,
This way we can choose when to upgrade our routers by just uploading new files to the central router and the next shcheduled run all routers shecduled will upgrade
/system upgrade upgrade-package-source
add address=x.x.x.x user=upgrade
Now since 6.45.1 we get authentication issues. we get below in the logs
06:05:36 system,error,critical login failure for user upgrade from x.x.x.x via winbox
06:05:36 system,error,critical login failure for user upgrade from x.x.x.x via winbox
Before we were running 6.44.3 with no issues we got below in the logs
02:00:00 system,info,account user upgrade logged in from x.x.x.x via winbox
02:00:00 system,info,account user upgrade logged in from x.x.x.x via winbox
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 7:57 am
by le1
Hello, I have problem with radius server authentication

hotspot,info,debug {MAC Address} (192.168.88.18): login failed: RADIUS server is not responding
hotspot,info,debug {MAC Address} (192.168.88.18): trying to log in by http-pap
When will you fix this problem?
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 8:27 am
by emils
RADIUS authentication issue is already fixed in the latest beta. We will try to release a new stable version next week with a few fixes.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 8:42 am
by Elans
spacex
nmt1900
Make sure that your monitored device "IP-SNMP communities" and The Dude "server settings" SNMP custom profile does not have any mismatch.
There is no mismatch and these community settings have been used for long time. Only Dude fails and it worked fine with 6.44.3. After testing it looks like only way to get it work with Dude is to use SNMPv2c or SNMPv1.
Can not reproduce your described problem, only with mismatched configuration. Have you tried to create new SNMP profile in The Dude and/or IP-SNMP communities? There must be something specific, if problem persist, you may try to send your supout.rif file to
support@mikrotik.com.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 8:43 am
by skylark
The issue with login via auto-upgrade feature is reproduced and will be fixed in upcoming RouterOS versions.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 9:31 am
by nostromog
It hangs in some initial script that tries to modify ipsec policies depending on dynamic local ip, it hangs on "/ export" or "/ip ipsec <whatever>". I can't generate a supout because it hangs

Have you tried to reset the machine to defaults before or better after upgrade to 6.45.1 and then manually create the IPsec configuration from the export rather than letting the upgrade script do that? This clearly cannot be used on the production machine but it should at least confirm that the IPsec part is the trigger, so you could be able to remove the IPsec configuration on the production machine before the upgrade if you can provide some other means to access it remotely (ssh, https) and recreate the IPsec part after the upgrade.
Thanks!!! It had not occurred to me that this might work, because when it first happened I downgraded, disabled the security package and upgraded again in the hope that this would allow me to re-enable and proceed. This worked, but re-enabling brought back the problem.
This machine is production but not really remote, no concern about loosing access. The only concern was downtime, but I did the whole operation yesterday during the night.
I did what you suggested: upgraded, went back to default configuration, re-executed the relevant parts of the export and I'm now in 6.45.1 I tried to restore a backup before but the problem reproduced, so re-executing from a export script was the winner.
The suggestion from support to netinstall would have amounted to much more work: first netinstall itself, then re-creating the configuration in exactly the same way, so basically I would have done to do the same.
Other than that, a support.rif of the state before upgrade should be enough for support to simulate the same process at their end.
Support did not asked me that, but they could find the problem (some corruption of the configuration created by some previous version, maybe a test with a beta) just by looking into a backup.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 9:57 am
by chubbs596
The issue with login via auto-upgrade feature is reproduced and will be fixed in upcoming RouterOS versions.
Thanks Guys
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 11:26 am
by NetVicious
As I posted before I had (as others) problems with GRE with this new version of RouterOS. In my case I'm using pptp VPN tunnels.
I have a master router acting as pptp Server and some other devices acting as pptp client.
2 of that clients had problems trying to connect to the pptp server after the 6.45.1 upgrade. After a downgrade all was OK another time. 3 other clients with the same configuration and hardware had no problems after the upgrade. So something strange was somewhere.
I discovered the problem was on the helper service for the pptp service on
IP / Firewall / Service Ports
On the routers with problems I had on the pptp item the 1723 port. That item was in red. That show me the tip to try removing the port on that item. I don't remember to add that port so it should be there from a lot of years ago when it was a default setting.
After that change pptp worked perfectly another time after the 6.45.1 upgrade.
Obviously this fix should work only for pptp VPN tunnels. For other setups that use GRE you should add
ONE of the fixes posted on this thread:
/ip firewall filter add chain=input action=accept protocol=gre src-address=
/ip firewall raw add action=notrack chain=prerouting protocol=gre
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 12:35 pm
by GambarottoM
Hi everyone,
I have a problem with queue and idle timeout in my default profile with radius authaticated users.
When a user try to login with the radius authetication (this one works for me), he will use my default user profile.
BUT he won't get my custom IDLE-TIMEOUT and won't create a NEW QUEUE in queues list, that are both in my user default profile.
If I use a local user with the same user profile, I don't have this problem.
If I use different parameters, I tried for example "keepalive-timeout", they will work as usual.
I don't know why, but these two paramethers are skipped in the authetication process with radius.
In addition to that my radius doesn't provide these two paramethers...
Problem only in v.6.45.1, in v6.44.3 (my previous version) all ok.
Thanks
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 12:51 pm
by nmt1900
spacex
nmt1900
Make sure that your monitored device "IP-SNMP communities" and The Dude "server settings" SNMP custom profile does not have any mismatch.
There is no mismatch and these community settings have been used for long time. Only Dude fails and it worked fine with 6.44.3. After testing it looks like only way to get it work with Dude is to use SNMPv2c or SNMPv1.
Can not reproduce your described problem, only with mismatched configuration. Have you tried to create new SNMP profile in The Dude and/or IP-SNMP communities? There must be something specific, if problem persist, you may try to send your supout.rif file to
support@mikrotik.com.
Problem persists even after SNMP settings are reconfigured on both sides - this has been tested on RB450Gx4, RB750Gr3 and CHR as Dude servers (3 different architectures). I sent supout files.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 1:39 pm
by buset1974
having problem upgrading hAP lite to 6.45.1 from 6.44.2
"system, error not enough space for upgrade."
thx
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 2:00 pm
by mkx
having problem upgrading hAP lite to 6.45.1 from 6.44.2
"system, error not enough space for upgrade."
In order to upgrade ROS, your hAP lite needs at least some 14MB RAM free (possibly even more) and around 1MB hdd free. Both are displayed using command
/system resource print (fields
free-memory and
free-hdd-space respectively).
If your RAM is low, try to reboot device (in case there are some processes which incrementally consume RAM, such as connection tracking or dynamic address lists). If hdd is low, try to remove some files which might occupy space - check output of
/file print).
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 3:08 pm
by le1
RADIUS authentication issue is already fixed in the latest beta. We will try to release a new stable version next week with a few fixes.
Thnx a lot

Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 3:30 pm
by dk5980
I am having 350 plus hotspot locations as my clients and hAP lite is being used almost @ 50 locations, and they got updated automatic. Now from every of those location I am getting complaints that hotspot login page is not coming automatically. user need to put the hotspot gateway ip or hotspot dns address in address bar of browser.
please resolve it ASAP, or suggest some work around.
I am having no such problem in rb850gx2, or rb450 or even hAP AC lite, all other routers are seems ok with this upgrade with as hotspot gateway.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 3:43 pm
by freemannnn
I am having 350 plus hotspot locations as my clients and hAP lite is being used almost @ 50 locations, and they got updated automatic. Now from every of those location I am getting complaints that hotspot login page is not coming automatically. user need to put the hotspot gateway ip or hotspot dns address in address bar of browser.
please resolve it ASAP, or suggest some work around.
I am having no such problem in rb850gx2, or rb450 or even hAP AC lite, all other routers are seems ok with this upgrade with as hotspot gateway.
updated automatic????? there is not such option in ros. maybe you have a script that does that. disable it.
why you update all business customers at once at the first day of ROS release? update one check-wait everything is ok and after do the others.
when something works dont touch it!
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 3:48 pm
by STEPHANVS
Download/Upload counters showed way off values in interface window, zero activity on my transmission server, higher CPU usage. All on an RB951G-2HnD. Rolled back to 6.44.3 for now.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 4:49 pm
by dk5980
I am having 350 plus hotspot locations as my clients and hAP lite is being used almost @ 50 locations, and they got updated automatic. Now from every of those location I am getting complaints that hotspot login page is not coming automatically. user need to put the hotspot gateway ip or hotspot dns address in address bar of browser.
please resolve it ASAP, or suggest some work around.
I am having no such problem in rb850gx2, or rb450 or even hAP AC lite, all other routers are seems ok with this upgrade with as hotspot gateway.
updated automatic????? there is not such option in ros. maybe you have a script that does that. disable it.
why you update all business customers at once at the first day of ROS release? update one check-wait everything is ok and after do the others.
when something works dont touch it!
Yes, because of script.
I did not run the script on first day, it was yesterday, and till then nobody complained the issue. Yesterday evening when i got to know the issue from several clients one by one etc then I took the notice. because other than hAP lite router, no one else complained till now and everything is working fine in them.
Please suggest me something . I cant make downgrade them.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 5:23 pm
by bnw
*) fetch - added SFTP support;
Good news !
Any way to use SSH key instead of password for login phase ?
Thank you !
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 5:39 pm
by osc86
Any updates regarding the SNMPv3 PrivAuth <-> Dude Issue?
For sure there's something wrong, I set up a new dude server and this "bad packet" error happens on all my devices running 6.45.1, LibreNMS works fine, though.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 7:28 pm
by NetVicious
Yes, because of script.
I did not run the script on first day, it was yesterday, and till then nobody complained the issue. Yesterday evening when i got to know the issue from several clients one by one etc then I took the notice. because other than hAP lite router, no one else complained till now and everything is working fine in them.
Please suggest me something . I cant make downgrade them.
You have remote access from your office to each device?
You can launch within the RouterOS api a downgrade command for each device at the same time.
I don't have the downgrade option on my
mtkManager but it can be easily added.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 8:25 pm
by nostromog
In order to upgrade ROS, your hAP lite needs at least some 14MB RAM free (possibly even more) and around 1MB hdd free. Both are displayed using command /system resource print (fields free-memory and free-hdd-space respectively).
If your RAM is low, try to reboot device (in case there are some processes which incrementally consume RAM, such as connection tracking or dynamic address lists). If hdd is low, try to remove some files which might occupy space - check output of /file print).
I wonder if those two short paragraphs by mkx should be present as a footnote in every new release announcement, subtituting hAP lite -> device

It would save some bad experience for users, and some work for support.
Re: v6.45.1 [stable] is released!
Posted: Fri Jul 05, 2019 9:20 pm
by vb99
my web proxy not work on this version. may somebody give me help?
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 12:40 am
by waeel
Hi support
When update 6.45.1 dont log in via api user or password erro
can you help me pls
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 12:55 am
by sindy
read previous posts in this topic, search for "api".
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 1:00 am
by eworm
I have serve issues with all my IPSec responders. As far as I can tell about half of my IPSec initiator devices do not get addresses from mode-config.
Not sure about the details. Anybody else seen this?
One after another the IPSec links came up without any configuration change. Finally today (after four days) every single link is up.
I can no longer reproduce - this looks as reliable as before the update. My guess is that any state data was corrupted on update and replaced successively later on.
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 9:10 am
by Grant
Hello!
after upgrading to version 6.45.1, power wi-fi lowered, permanent disconnects appeared, especially in the next room
device hAP ac lite
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 2:10 pm
by tesme33
In order to upgrade ROS, your hAP lite needs at least some 14MB RAM free (possibly even more) and around 1MB hdd free. Both are displayed using command /system resource print (fields free-memory and free-hdd-space respectively).
If your RAM is low, try to reboot device (in case there are some processes which incrementally consume RAM, such as connection tracking or dynamic address lists). If hdd is low, try to remove some files which might occupy space - check output of /file print).
I wonder if those two short paragraphs by mkx should be present as a footnote in every new release announcement, subtituting hAP lite -> device

It would save some bad experience for users, and some work for support.
Hi @nostromog
i would say even with the paragraphs you are not able to make the upgrade.
I have no files at all on my haplite (2 pcs) and only a minimal config. One worked and one not.
So what now ?
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 3:02 pm
by salah
hi,
I upgrade my router from 6.43 to 6.45.1
i get a problem when I connect my laptop (win10) with 802.1x authentication to the router with dot1x server and user-manager enabled.
authentication method: Microsoft PEAP
secured pass: (EAP-MSCHAP V2)
I get this error (unknown authentication algorithm )
log:

Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 3:09 pm
by salah
having problem upgrading hAP lite to 6.45.1 from 6.44.2
"system, error not enough space for upgrade."
thx
copy everything from file to your computer, upgrade your router and get your file back to the router after upgrade .
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 4:29 pm
by pe1chl
having problem upgrading hAP lite to 6.45.1 from 6.44.2
copy everything from file to your computer, upgrade your router and get your file back to the router after upgrade .
When you have files on your hAP lite, you are doing something wrong! This is a low-end router that is not supposed to have files on it. There is no space.
I booted my hAP lite (which is not in active use) and upgraded it from 6.44.3 to 6.45.1 without any problem.
Before the upgrade it had 8mb RAM free and apparently that is enough.
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 5:17 pm
by dk5980
Yes, because of script.
I did not run the script on first day, it was yesterday, and till then nobody complained the issue. Yesterday evening when i got to know the issue from several clients one by one etc then I took the notice. because other than hAP lite router, no one else complained till now and everything is working fine in them.
Please suggest me something . I cant make downgrade them.
You have remote access from your office to each device?
You can launch within the RouterOS api a downgrade command for each device at the same time.
I don't have the downgrade option on my
mtkManager but it can be easily added.
Where I may get this mtkManager ?
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 8:49 pm
by Iwanche
Does someone have a problem with mac telnet login via neighbours?
Won't login with any user and pass or without pass, nor admin..
Re: v6.45.1 [stable] is released!
Posted: Sat Jul 06, 2019 10:07 pm
by mahadiapps
Dear Sir,
I have CCR 1036 8G-2S+ Router. When Router os update V6.45.1 ( stable) this code doesn't working, or login mikrotik router how to change please help.
<?php
/*****************************
*
* RouterOS PHP API class v1.5
* Author: Denis Basta
* Contributors:
* Nick Barnes
* Ben Menking (ben [at] infotechsc [dot] com)
* Jeremy Jefferson (http://jeremyj.com)
* Cristian Deluxe (djcristiandeluxe [at] gmail [dot] com)
*
* http://www.mikrotik.com
* http://wiki.mikrotik.com/wiki/API_PHP_class
*
******************************/
class routeros_api
{
var $debug = false; // Show debug information
var $error_no; // Variable for storing connection error number, if any
var $error_str; // Variable for storing connection error text, if any
var $attempts = 5; // Connection attempt count
var $connected = true; // Connection state
var $delay = 3; // Delay between connection attempts in seconds
var $port = 8728; // Port to connect to
var $timeout = 3; // Connection attempt timeout and data read timeout
var $socket; // Variable for storing socket resource
/**
* Print text for debug purposes
*
* @param string $text Text to print
*
* @return void
*/
function debug($text)
{
if ($this->debug)
echo $text . "\n";
}
/**
*
*
* @param string $length
*
* @return void
*/
function encode_length($length)
{
if ($length < 0x80) {
$length = chr($length);
} else if ($length < 0x4000) {
$length |= 0x8000;
$length = chr(($length >> 8) & 0xFF) . chr($length & 0xFF);
} else if ($length < 0x200000) {
$length |= 0xC00000;
$length = chr(($length >> 16) & 0xFF) . chr(($length >> 8) & 0xFF) . chr($length & 0xFF);
} else if ($length < 0x10000000) {
$length |= 0xE0000000;
$length = chr(($length >> 24) & 0xFF) . chr(($length >> 16) & 0xFF) . chr(($length >> 8) & 0xFF) . chr($length & 0xFF);
} else if ($length >= 0x10000000)
$length = chr(0xF0) . chr(($length >> 24) & 0xFF) . chr(($length >> 16) & 0xFF) . chr(($length >> 8) & 0xFF) . chr($length & 0xFF);
return $length;
}
/**
* Login to RouterOS
*
* @param string $ip Hostname (IP or domain) of the RouterOS server
* @param string $login The RouterOS username
* @param string $password The RouterOS password
*
* @return boolean If we are connected or not
*/
function connect($ip, $login, $password)
{
for ($ATTEMPT = 1; $ATTEMPT <= $this->attempts; $ATTEMPT++) {
$this->connected = false;
$this->debug('Connection attempt #' . $ATTEMPT . ' to ' . $ip . ':' . $this->port . '...');
$this->socket = @fsockopen($ip, $this->port, $this->error_no, $this->error_str, $this->timeout);
if ($this->socket) {
socket_set_timeout($this->socket, $this->timeout);
$this->write('/login');
$RESPONSE = $this->read(false);
if ($RESPONSE[0] == '!done') {
$MATCHES = array();
if (preg_match_all('/[^=]+/i', $RESPONSE[1], $MATCHES)) {
if ($MATCHES[0][0] == 'ret' && strlen($MATCHES[0][1]) == 32) {
$this->write('/login', false);
$this->write('=name=' . $login, false);
$this->write('=response=00' . md5(chr(0) . $password . pack('H*', $MATCHES[0][1])));
$RESPONSE = $this->read(false);
if ($RESPONSE[0] == '!done') {
$this->connected = true;
break;
}
}
}
}
fclose($this->socket);
}
sleep($this->delay);
}
if ($this->connected)
$this->debug('Connected...');
else
$this->debug('Error...');
return $this->connected;
}
/**
* Disconnect from RouterOS
*
* @return void
*/
function disconnect()
{
fclose($this->socket);
$this->connected = false;
$this->debug('Disconnected...');
}
/**
* Parse response from Router OS
*
* @param array $response Response data
*
* @return array Array with parsed data
*/
function parse_response($response)
{
if (is_array($response)) {
$PARSED = array();
$CURRENT = null;
$singlevalue = null;
foreach ($response as $x) {
if (in_array($x, array(
'!fatal',
'!re',
'!trap'
))) {
if ($x == '!re') {
$CURRENT =& $PARSED[];
} else
$CURRENT =& $PARSED[$x][];
} else if ($x != '!done') {
$MATCHES = array();
if (preg_match_all('/[^=]+/i', $x, $MATCHES)) {
if ($MATCHES[0][0] == 'ret') {
$singlevalue = $MATCHES[0][1];
}
$CURRENT[$MATCHES[0][0]] = (isset($MATCHES[0][1]) ? $MATCHES[0][1] : '');
}
}
}
if (empty($PARSED) && !is_null($singlevalue)) {
$PARSED = $singlevalue;
}
return $PARSED;
} else
return array();
}
/**
* Parse response from Router OS
*
* @param array $response Response data
*
* @return array Array with parsed data
*/
function parse_response4smarty($response)
{
if (is_array($response)) {
$PARSED = array();
$CURRENT = null;
$singlevalue = null;
foreach ($response as $x) {
if (in_array($x, array(
'!fatal',
'!re',
'!trap'
))) {
if ($x == '!re')
$CURRENT =& $PARSED[];
else
$CURRENT =& $PARSED[$x][];
} else if ($x != '!done') {
$MATCHES = array();
if (preg_match_all('/[^=]+/i', $x, $MATCHES)) {
if ($MATCHES[0][0] == 'ret') {
$singlevalue = $MATCHES[0][1];
}
$CURRENT[$MATCHES[0][0]] = (isset($MATCHES[0][1]) ? $MATCHES[0][1] : '');
}
}
}
foreach ($PARSED as $key => $value) {
$PARSED[$key] = $this->array_change_key_name($value);
}
return $PARSED;
if (empty($PARSED) && !is_null($singlevalue)) {
$PARSED = $singlevalue;
}
} else {
return array();
}
}
/**
* Change "-" and "/" from array key to "_"
*
* @param array $array Input array
*
* @return array Array with changed key names
*/
function array_change_key_name(&$array)
{
if (is_array($array)) {
foreach ($array as $k => $v) {
$tmp = str_replace("-", "_", $k);
$tmp = str_replace("/", "_", $tmp);
if ($tmp) {
$array_new[$tmp] = $v;
} else {
$array_new[$k] = $v;
}
}
return $array_new;
} else {
return $array;
}
}
/**
* Read data from Router OS
*
* @param boolean $parse Parse the data? default: true
*
* @return array Array with parsed or unparsed data
*/
function read($parse = true)
{
$RESPONSE = array();
$receiveddone = false;
while (true) {
// Read the first byte of input which gives us some or all of the length
// of the remaining reply.
$BYTE = ord(fread($this->socket, 1));
$LENGTH = 0;
// If the first bit is set then we need to remove the first four bits, shift left 8
// and then read another byte in.
// We repeat this for the second and third bits.
// If the fourth bit is set, we need to remove anything left in the first byte
// and then read in yet another byte.
if ($BYTE & 128) {
if (($BYTE & 192) == 128) {
$LENGTH = (($BYTE & 63) << 8) + ord(fread($this->socket, 1));
} else {
if (($BYTE & 224) == 192) {
$LENGTH = (($BYTE & 31) << 8) + ord(fread($this->socket, 1));
$LENGTH = ($LENGTH << 8) + ord(fread($this->socket, 1));
} else {
if (($BYTE & 240) == 224) {
$LENGTH = (($BYTE & 15) << 8) + ord(fread($this->socket, 1));
$LENGTH = ($LENGTH << 8) + ord(fread($this->socket, 1));
$LENGTH = ($LENGTH << 8) + ord(fread($this->socket, 1));
} else {
$LENGTH = ord(fread($this->socket, 1));
$LENGTH = ($LENGTH << 8) + ord(fread($this->socket, 1));
$LENGTH = ($LENGTH << 8) + ord(fread($this->socket, 1));
$LENGTH = ($LENGTH << 8) + ord(fread($this->socket, 1));
}
}
}
} else {
$LENGTH = $BYTE;
}
// If we have got more characters to read, read them in.
if ($LENGTH > 0) {
$_ = "";
$retlen = 0;
while ($retlen < $LENGTH) {
$toread = $LENGTH - $retlen;
$_ .= fread($this->socket, $toread);
$retlen = strlen($_);
}
$RESPONSE[] = $_;
$this->debug('>>> [' . $retlen . '/' . $LENGTH . '] bytes read.');
}
// If we get a !done, make a note of it.
if ($_ == "!done")
$receiveddone = true;
$STATUS = socket_get_status($this->socket);
if ($LENGTH > 0)
$this->debug('>>> [' . $LENGTH . ', ' . $STATUS['unread_bytes'] . ']' . $_);
if ((!$this->connected && !$STATUS['unread_bytes']) || ($this->connected && !$STATUS['unread_bytes'] && $receiveddone))
break;
}
if ($parse)
$RESPONSE = $this->parse_response($RESPONSE);
return $RESPONSE;
}
/**
* Write (send) data to Router OS
*
* @param string $command A string with the command to send
* @param mixed $param2 If we set an integer, the command will send this data as a "tag"
* If we set it to boolean true, the funcion will send the comand and finish
* If we set it to boolean false, the funcion will send the comand and wait for next command
* Default: true
*
* @return boolean Return false if no command especified
*/
function write($command, $param2 = true)
{
if ($command) {
$data = explode("\n", $command);
foreach ($data as $com) {
$com = trim($com);
fwrite($this->socket, $this->encode_length(strlen($com)) . $com);
$this->debug('<<< [' . strlen($com) . '] ' . $com);
}
if (gettype($param2) == 'integer') {
fwrite($this->socket, $this->encode_length(strlen('.tag=' . $param2)) . '.tag=' . $param2 . chr(0));
$this->debug('<<< [' . strlen('.tag=' . $param2) . '] .tag=' . $param2);
} else if (gettype($param2) == 'boolean')
fwrite($this->socket, ($param2 ? chr(0) : ''));
return true;
} else
return false;
}
/**
* Write (send) data to Router OS
*
* @param string $com A string with the command to send
* @param array $arr An array with arguments or queries
*
* @return array Array with parsed
*/
function comm($com, $arr = array())
{
$count = count($arr);
$this->write($com, !$arr);
$i = 0;
foreach ($arr as $k => $v) {
switch ($k[0]) {
case "?":
$el = "$k=$v";
break;
case "~":
$el = "$k~$v";
break;
default:
$el = "=$k=$v";
break;
}
$last = ($i++ == $count - 1);
$this->write($el, $last);
}
return $this->read();
}
}
?>